The Issue of Informatized Conflict
| ✅ Paper Type: Free Essay | ✅ Subject: Military |
| ✅ Wordcount: 4472 words | ✅ Published: 18 Sep 2017 |
Charles H. Rybeck, Lanny R. Cornwell, & Philip M. Sagan
It took the remilitarization of the Rhineland in 1936 to awaken many to the threat of the Nazis. In 1957, it took Sputnik to awaken the US to the Soviet threat in space. It took 9/11 to awaken many to the threat of violent Islamist extremism. And it took the Underwear Bomber of Christmas Day 2009 to awaken the White House to the inadequacy of the way the US used its Terrorism Watchlist.
What will it take to awaken us to the threat of what the Chinese insightfully call “Informatized Conflict[1]?”
Will we embolden our adversaries through an ineffectual response as the world did when facing the emerging Nazi threat? Or will we respond as decisively and with as much foresight as we did to Sputnik?
What will it take to align the United States Government (USG, used here as synonymous with “whole of Government” as an enterprise construct) and its allies to take effective countermeasures to prevail in Informatized Conflict? In this article, we outline a non-partisan, USG-led strategy for security in the face of that challenge.
“Information Technology,” the quaint and already outdated concept of “IT,” fails to capture the digital dimension of our world in the Information Age. The concept harkens back to the now-distant days when IT was a sequestered, relatively unimportant, compartment of our world. CIOs reported to CFOs because CEOs pigeonholed computers as simple aids to accounting. In reality, though, as anyone with a smart phone knows, the digital dimension is now integral to every aspect of business and societal interaction on a global scale.
Each day we wake up in a world of active Informatized Conflict. Unseen battles are being waged all around us. After the Chinese penetrated our military weapons supply chain, after the North Koreans exposed our corporate vulnerabilities, and after the Russians influenced our national media in the 2016 Presidential Election, how is it that we haven’t responded strategically to this clear and present danger? What catastrophe would we have to experience to take the steps necessary for our own defense?
Sadly, the USG and our entire National Security Enterprise (which includes all stakeholders, public and private) are failing to directly confront the digital threat because it is not constituted to see this issue. Our institutions look at the world as it was, not as it is, and not as it is inevitably becoming in the rapidly emerging world of the Internet of Things (IoT), where machine learning will play an essential role in organizing the growing sea of information in which we live.
Every tool we use in national security (from weapons to intelligence to diplomacy), in commerce, and in governance now rests on a rapidly evolving digital foundation. Today we must run to keep up, and tomorrow we will be required to run even faster. This challenge to run is, unfortunately, in an area where we have seldom managed to crawl and our nation’s leaders have not fully recognized that reality at the highest levels. Senior executives are only beginning to realize that our digital challenges have become mission-critical, that they defy our routine acquisition processes, and that they are too consequential to be left to technologists and acquisition specialists, alone.
The pressing need for consideration of Informatized Conflict by non-technologists prompted us to translate what have been internal Department of Defense (DoD) and Intelligence Community (IC), IT-based debates into unclassified laymen’s terms for consideration by informed influencers. This article was written to (1) identify key, progress-limiting issues on which the Executive Branch and Congress need to act, (2) offer a unifying and non-partisan strategy to protect Security and Freedom. In Part II of this series uses two specific examples to illustrate the execution of this proposed strategy.
Responding to Global Disruption: How do We Need to Change the Way We Fulfill our National Security Mission?
The digital dimension is enhancing and disrupting the fabric of life in every society where modern technology is present. Walter Russell Mead’s Blue Social Model[2] describes the slow-motion collapse of that part of the 20th Century’s legacy is now accelerating in ways that will likely usher in an historic realignment. This realignment will, of necessity, change the frameworks within which America provides for its security, including how it acquires the goods and services it uses in that effort. 2017’s national and international news is unfolding so feverishly that the non-partisan Joint action recommended in this article is in constant jeopardy of becoming overcome by events.
As Mead points out, Donald Trump’s election can best be understood as part of the Blue Social Model’s collapse. TAI readers will not be shocked to hear that Government, Industry, and Labor leaders have all, in their rush to preserve the old order, ignored the digital dimension’s National Security imperatives. Despite all the Government’s talk about the Internet & Cybersecurity and all its investment in IT & Cyber, our National Security Enterprise has yet to reorient its priorities or its budget to prepare for Informatized Conflict.
Right now, our Government has a unique opportunity to reorient the structure, flow, and management of the information for the National Security Enterprise in ways that both ensure the security of our future and reduce the cost of our defense.[3] We have not yet recognized that-even though our challenges have their roots in the technology arena-business-as-usual technological solutions alone will not address these challenges. USG decision makers and influencers, from the Executive Branch to Congress to our citizenry as a whole, will have to consider and adopt a Joint strategy in order to realize the benefits of this digital reorientation. Of course, this will take us outside our national comfort zone, but, given the Informatized Conflict threat, the alternative of continuing with business-as-usual is unthinkable.
Wise observers have pointed out that overreaction to catastrophic attack is likely to jeopardize our democracy. So, prevention of such attacks should be a rallying point for citizens of every political persuasion. And we should protect our capacity for non-partisan and bipartisan cooperation on confronting our vulnerabilities as one of our strongest National Security assets. Only the Trump Administration’s actions to preserve and rebuild trust across the National Security Enterprise can make that cooperation possible.
Vision for a New National Security Jointness:

Figure 1: The Joint National Security Enterprise: Combining Capabilities of the DoD, IC, and International Partners
Source: USD(I)
In the US, we entrust our frontline National Defense leadership to the DoD and the IC, two interconnected but separate chains of command. These entities are chartered to deliver kinetic and non-kinetic capabilities. Only the Commander-in-Chief (POTUS) controls both.
In 2009, Lt Gen James Clapper, as Under Secretary of Defense for Intelligence [USD(I)] combined his focus on Intelligence, Surveillance, and Reconnaissance (ISR) with all projections of national power that are informed by ISR in a vision for Jointness. This vision (see Figure 1.) has yet to be implemented, but it provides the basis necessary for C4ISR Fusion (Command, Control, Communications, Computers, Intelligence, Surveillance, and Reconnaissance). This vision summarizes what the DoD and the IC agree on in theory. They agree on “Jointness” and “Fusion” in the fields of intelligence, military operations, cybersecurity, and counterterrorism.[4]
“Jointness” has a proud and successful history as a strategy for the US Armed Forces. But here we use the term “Joint” to refer not only to the combined Armed Services but to the unified actions of all the DoD, IC, and other stakeholders-and ever-shifting alliances-whose efforts combine in pursuit of National Security with all the instruments of national power.
“Fusion” here combines data, data science, and data services to achieve security objectives first outlined by the bipartisan 9/11 Commission. We depend on this Fusion at every stage of conflict. For example, modern ISR depends on Upstream Data Fusion (UDF), not always having to wait for cumbersome sequences to produce a fully-vetted finished document. Similarly, active conflict with near-peer adversaries demands kinetic responses only possible via Fusion-based, Machine-to-Machine (M2M) interoperability. A concerted national application of Jointness and Fusion can break the deadlock that is keeping us from doing what we know we need to do at the enterprise-level to defend ourselves in a world of Informatized Conflict. That Jointness can only be achieved by bringing together the appropriate teams, at the appropriate levels, to ensure a clear commander’s intent is realized.
Our Three Indispensable Mission-Critical Teams
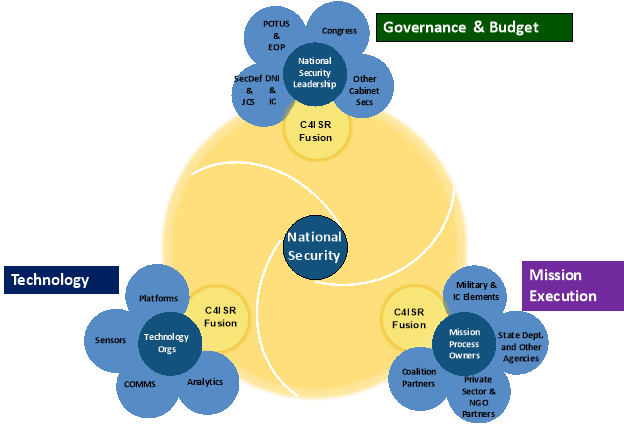
Figure 2: The National Security Enterprise’s Three Mission-Critical Teams
Source: DMI
Three Mission-Critical Teams combine to form the National Security Enterprise and fulfill its mission. The Government teams (Governance & Budget, Mission Execution, and Technology) perform functions analogous to their three familiar private sector equivalents (i.e., the CEO, COO, and CIO organizations). The obvious differences between the Government’s organization and the private sector (for example, the shared powers of Congress and POTUS) are useful in understanding why common-sense solutions and efficiencies adopted almost universally in the private sector have been rejected within the Government. C4ISR Fusion connects the three Mission-Critical Teams for Informatized Conflict.
Acquisition to Support USG Innovation?
Eisenhower’s farewell address cautioned us to be wary as well as transparent in how we contract with the military-industrial base to improve capabilities. Despite yeoman efforts by the Executive Branch and Congress, America’s system for acquisition has not matched Eisenhower’s challenge nor has it kept up with technology’s structural transformation. Platforms, sensors, and systems are undergoing widely reported changes, but the USG meet the current acquisition challenge only by understanding the “molecular structure” of the information or digital substrate underlying them all.
Without the discipline imposed by what the private sector calls a “business case,” the USG has become famous for failed large-scale technology initiatives.[5] Fortunately, though, new, private-sector innovations are creating opportunities to change how the Government conducts its National Security business.
Industry observers are all aware that software development has undergone an historic transformation from grand, multi-year “Waterfalls” to modest, short-term “Agile” sprints. “DevOps” is now coming into use to describe “software DEVelopment” and “information technology OPerationS” as a way of accelerating the building, testing, and releasing software. Famously taking advantage of microservices and “as-a-service” infrastructure, private sector leaders (such as Netflix and Uber) are currently showing how new software can be delivered hourly.
In contrast, fielding software enhancements in National Security now typically takes years. The USG is adopting Agile development-but within enterprise strictures that are preventing the implementation of many of its most potent benefits.
Responding to these global, private sector-led changes, Congress has mandated acquisition change in the National Defense Authorization Acts of 2016 and 2017. [6]Â Although such reform has been a perennial subject of conversation, Secretary of Defense Mattis has an opportunity to work with a receptive Administration and Congressional leaders like the Chairmen of the Senate and House Armed Services Committees, Senator John McCain (R-AZ) and Rep. Mac Thornberry (R-TX), to fundamentally reorient acquisition. In the past, the USG focused primarily on procuring existing products, services, and capabilities to meet known “requirements.” Now, the USG needs to build the “inherently Governmental” internal competency to lead a new way of doing business: continuous engineering to take advantage of evolving technology in a data-centric context and to confront evolving threats.
In confronting the current strategic and acquisition challenge, the Trump Administration will need to avoid the pitfalls of commercial conflicts of interest, bureaucratic overreach, and unnecessary partisanship. In a dynamic commercial environment involving many vendors offering to sell partial solutions to the USG, the Administration will need to improve its acquisition and orchestration functions.
What does an informed USG senior executive need to know about the infinite array of National Security technological and programmatic detail in order to affect such a consequential change? At one level, it is quite simple:
- Private Sector best practices can guide, regulate, and execute the many functions that are not unique to the USG.
- Key mission areas, in contrast, demand unique and USG-specific intervention. US law often refers to this as “inherently Governmental” and specifies how it needs to be handled. Private Sector best practices, here, are inadequate to meet USG needs.
This simple distinction can be usefully applied to our current Informatized Conflict challenge.
Commander’s Intent/ Congressional Intent/ National Strategy: We Already Know What Works
The Trump Administration should begin immediately to remedy the gridlock inherent in so much of the USG’s preparation for Informatized Conflict. The Executive Office of the President (EOP) could mobilize the leaders of Government’s three Mission-Critical Teams (Governance & Budget, Mission Execution, and Technology) across the entire National Security Enterprise. Together, the three Mission-Critical Teams could champion “Tightly Aligned” core capabilities to enable enterprise functionality and innovation at the “Loosely Coupled” edge.

Figure 3: Tightly Aligned/ Loosely Coupled as an alternative to today’s dysfunction
and as a Winning Joint Strategy in Informatized Conflict
While the Tightly Aligned/ Loosely Coupled approach originated as an engineering concept, it has been successfully applied in concert by the three private sector equivalents of the Mission-Critical Teams to guide similar foundational, Internet-dependent initiatives. Major retailers and service delivery firms (famously, Wal-Mart in the 1990s and Netflix in the 2000s, for example) rebuilt their supply chains using this approach. The Google Android used on smartphones, tablets, and other devices-the operating system (OS) with the world’s largest installed base-is an open source example of this strategy in action.
The Tightly Aligned/ Loosely Coupled strategy applied to the USG’s digital assets can be what Ernest May and Philip Zelikow called a Capital “P” Policy[7], a redirection around which the country unites over a long timespan and across political divides. This and subsequent Administrations will need a rigorous “Mission/Business Case” to sustain alignment among these three Mission-Critical Teams. Fortunately, the mission benefits are so powerful and the cost savings so dramatic that the “Mission/Business Case” could be strong enough to overcome the entrenched interests who will, of course, fight it with all the tools at their disposal. The essence of the Tightly Aligned/ Loosely Coupled strategy is to agree on those few principles, policies, and standards necessary for the enterprise to function as a unified whole. Then operational units and individual programs can be freed to innovate “at the edge” in whatever ways best serve their individual missions.
Who Needs to Do What?
What we are proposing is an approach inspired by extraordinary systems thinkers from each of the three Mission-Critical Teams. Here we give examples with an emphasis on those representing the Governance & Budget and Mission Execution teams. The only technologist listed here is Dr. Cerf:
- Andy Marshall (retired leader of the Defense Department’s Office of Net Assessment)
- Gen Mike Hayden (retired after leading NSA and CIA)
- Philip Zelikow (former executive director of both the Markle Foundation task force on National Security in the Information Age and then the 9/11 Commission; later Counselor of the Department of State under Secretary Condoleezza Rice)
- The late Ernie May (senior advisor to the 9/11 Commission)
- Michèle Flournoy (former Under Secretary of Defense for Policy and now head of the Center for a New American Security)
- Gen Paul Selva (the Vice Chairman of the Joint Chiefs of Staff)
- Vint Cerf (the co-inventor of TCP/IP, the messaging protocol that underlies the entire Internet)
They and we have found that few Government executives have the cross-functional experience to fully appreciate their counterparts’ frames of reference. But the kind of changes that the USG needs now can only be made by aligning the strategies of all of the three Mission-Critical Teams.
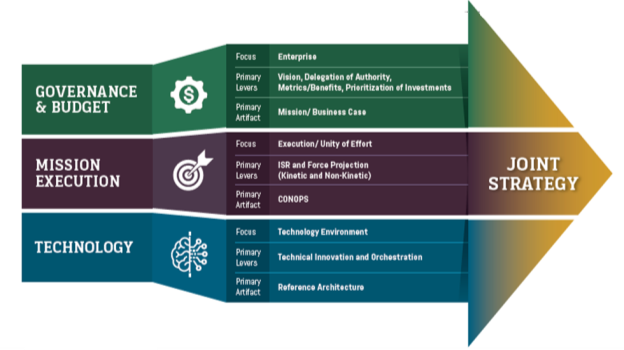

Figure 4: Aligning the Three Mission-Critical Teams
Source: DMI
The three Mission-Critical Teams bring very different foci, levers, and artifacts to the fight. These, in turn, depend on distinctive disciplines, equities, goals, methodologies, timetables, and metrics. In order for the teams to align, each need to accommodate the others’ demands and battle rhythms.
A Call to Action
President Dwight Eisenhower personally led the response to Sputnik. Among a series of coordinated initiatives, he formed the Advanced Research Projects Agency (ARPA) which changed the Government’s approach to procurement of high risk, high payoff advanced technology, ensured US leadership in the Space Race, and funded what eventually became the Internet. Eisenhower demonstrated the power of senior executive decisions in combining the three Mission-Critical Teams under the coordination of the EOP.
This article has proposed how the three Mission-Critical Teams Necessary for Security (Governance & Budget, Mission Execution, and Technology) can mobilize around a Tightly Aligned/ Loosely Coupled strategy. We have specified roles and responsibilities in language understandable to each of those teams. We have proposed a framework that enables serious, public consideration of issues that have been ignored, enables senior executives to take decisive Joint action, and enables them to authorize unclassified metrics for assessing progress in classified realms.[8]
Do we have to wait until adversaries inflict catastrophic damage before we take the steps that we already know we need? Will we allow ourselves to be incapacitated by internal divisions? In advance of the unthinkable, can we do what it takes to provide for the common defense in this Age of Informatized Conflict?
Charles H. Rybeck, Lanny R. Cornwell, and Philip M. Sagan are Senior Advisors to the Intelligence Community and the Defense Department on Enterprise Engineering issues. They are CEO, COO, and CTO of Digital Mobilizations, Inc. (DMI).
This is Part II of an Occasional Special Series
DRAFT IN PROCESS: Not Releasable in Any Form
This requires Prepublication Review before official submission
The Figures are in this draft for content only. They are being recreated in forms suitable for publication.
This is a continuation of theWhat Will It Take? Part I of an Occasional TAI Special Series.
Tightly Aligned/ Loosely Coupled Strategy in Action: Two Illustrative Examples
Charles H. Rybeck, Lanny R. Cornwell, & Philip M. Sagan
The Tightly Aligned/ Loosely Coupled strategy calls for budgetary, operational, and technology changes, but in this article, we only introduce the strategy in broad outline using two representative examples of where the USG has already successfully begun. These two examples underscore the role of the combined three Mission-Critical Teams within the Government in initiatives that require broad popular support.
Below we explore two examples in order to illustrate the challenge facing the USG, to show how pockets of excellence within the USG have already pointed the way forward, to demonstrate how the challenge of the digital dimension demands different USG responses, and to underscore what, concretely, will need to be done by the USG. Many achievements are classified, legitimately and necessarily protected from public discussion. But any digital strategy for National Security can and must be agreed upon at the unclassified level, sustaining widespread public support on the basis of sound arguments that include a full defense of our privacy and civil liberties. For that reason, we consider two pathfinding efforts, acknowledging their strengths and sketching what needs to be done next.
Our System Can Work: We’ve Shown We Can Crawl
We assess the US response to the challenge of the digital dimension as requiring a progression from “Crawl” to “Walk” to “Run.” US visions for future defense such as the Third Offset, Integrated Intelligence, Cyber Security, Data-to-Decisions (D2D), and Fusion Warfare all depend on this digital foundation. For the last decade, for example, the DoD has been guided by the Anti-Access/Area Denial (A2/AD) construct in planning to confront near-peer adversaries. A2/AD will also need to adjust its view of platforms, sensors, and weapons to accommodate the kinetic and non-kinetic implications of this new digital foundation.
Fortunately, much groundwork for this mobilization is already being laid at the Federal level. We can already point to many successes at the Crawl stage. Two examples can illuminate how consequential these decisions can be, how the role of the USG will need to be tailored to the problems, and how much further we have to go in order to Walk and Run.
- Example #1 Modernizing Infrastructure: In 2012, the IC recognized how it was consuming and delivering IT hardware, software, and services in ways that were unnecessarily inferior to the private sector. They awoke to the fact that the Government’s acquisition approach was handcuffing every aspect of National Security. The Congress, the IC, and the Administration supported the Central Intelligence Agency (CIA) in taking the lead in this initiative. They all deserve credit for the joint effort.
- The CIA reoriented its office of the CIO. It created a Commercial Cloud Services (C2S) contract to end CIA reliance on internal, outmoded expenditures and shift to purchasing infrastructure services as a utility. And it put the CIO under a new Directorate of Digital Innovation (DDI) to better link it with Mission functions.
- The contract enables a new, market-based model for acquiring enterprise-level software. C2S-based applications are licensed with fees to software vendors paid on the basis of the utilization of their products. This marketplace allows competing products to be evaluated and adopted by users in their day-to-day decisions as to how best meet the requirements of a specific problem. In the rapidly evolving data craft of the Internet, this method is far more adaptive and effective than a pre-determined, “one size fits all solution” imposed by a centralized bureaucracy.
- In technical terms, the IC is shifting much of its infrastructure costs from CAPEX (Capital Expenditure) to OPEX (Operational Expenditure), eliminating recurring CAPEX, paying only for services as needed, and arranging to stay current with hardware and software innovation in ways that were impossible in the old business model.
The success of the CIA’s C2S initiative results from the Agency’s recognition that the effective use of commercial market investments, technologies, and business processes can result in highly effective application of all too precious tax-payer capital, avoiding ineffective, costly duplication. The result of the Agency’s strategy has been improved mission effectiveness while freeing scarce technology development funds to meet those needs that are truly unique to the Agency’s mission.
- Example #2 Modernizing Knowledge Management (KM):
- In marked contrast to Infrastructure, the management of information within Federal systems was recognized by the IC as an inherently Governmental function, a core competence that should not be outsourced.
- Accepting that responsibility, the National Security Agency (NSA) took the lead in the Smart Data Initiative to identify what standardized labeling of packets of information are necessary in a modern digital environment.
- The first results, an Enterprise Data Header (EDH), was a signal achievement, admittedly and intentionally minimalist, but sufficient to enable the IC Cloud in its Crawl phase.
In both these examples, Infrastructure and KM, success was achieved only because the organizations involved, specifically the Congress, the Administration, ODNI, CIA, and NSA all aligned their three Mission-Critical Teams in the service of a new strategic direction.
But Can We Walk & Run?
In order to achieve mission benefits we’ll need to stop mistaking Easy for Hard and Complex for Simple. We have selected these two specific Crawl success stories because they also illustrate the executive decisions that need to be made today if we are going to Walk and Run tomorrow. In the case of infrastructure-which can best be thought of as plumbing-something relatively straightforward is being made unnecessarily complex within the DoD acquisition and planning apparatus. In the case of KM, many USG Departments & Agencies-including the IC & DoD-are mistaking KM as a simple issue. The USG is failing to come to grips with something inherently difficult by, in some cases, inaccurately imagining it is easy: “if we just build the plumbing, everything else will take care of itself”. It is only by effectively structuring and managing information (KM) that the USG will induce the digital dimension to yield its mission benefits.
In both cases (Infrastructure and KM) necessary but insufficient actions have been taken. Creating Cloud repositories for data and minimal metadata standards are achievements, but, in themselves, they cannot produce the Mission Benefits that are needed and that have been promised. Sadly, many executives have bought into an “automagic fallacy” that these Crawl phase activities would automagically produce Walk and Run results.
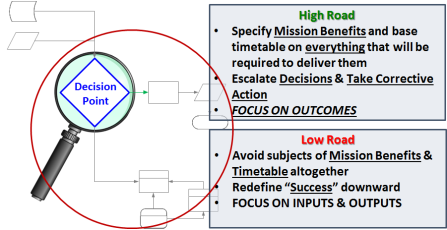
Figure 5: What is a Responsible Executive to Do?
Source: DMI
Lower level Government employees are left holding the bag. They are forced to describe classic “Quick Wins” and “low-hanging fruit” because it is only their boss’ bosses who are empowered to make the tough choices and substantial investments that will be required to produce the promised Mission Benefits. In the Agile development environment, where development of software continues apace as long as lower level Government “product owners” approve incremental progress, mission-critical decisions and investments are often postponed indefinitely.
The impediments to the High Road are so formidable that thousands of National Security employees and contractors have adopted the Low Road. The distinction depicted in Figure 5. has actually been rejected by USG employees because it disparages the Low Road. “That is the strategy we’ve adopted, and we need to promote it.”
- Example #1 Enterprise Infrastructure: Private Sector Best Practices Leading the Way for Government Action
Due to the disconnect between the DoD and the IC, Infrastructure Modernization is currently being held back at the National Security Enterprise level. Private sector solutions will need to drive this partnership.
- The DoD and its Armed Services are resisting the massive budgetary/acquisition changes needed to implement the CIA-led strategy.
- Only the Commander’s Intent will be strong enough to clear this impediment.
- POTUS does not need to wait for a catastrophe to prompt this solution.
- Example #2 Enterprise Knowledge Management (KM): Government Active Management of a Modularized, Multi-Vendor Competitive Environment for Innovation
At the same time that a sound foundation for KM was being laid through the establishment of IC data standards in the EDH, two basic strategies for the acquisition of knowledge exploitation technology were utilized. We’ve termed the first approach The Hedgehog and the second The Fox in honor of Berlin’s 1953 essay on Tolstoy and the philosophy of history, which begins quoting the ancient Greek poet, Archilochus, who wrote “The fox knows many things, but the hedgehog knows one big thing.”
The Hedgehog. The hedgehog strategy entailed the acquisition of an all-inclusive solution from a single vendor, what we can think of as a highly-advanced knowledge appliance[9], a comprehensive solution that combined hardware, software, and a particular way of thinking about knowledge, problems, questions, and answers. This approach outsourced all to a single supplier. It fit the existing procurement system well because it focused on a single, big procurement decision.
The Fox. The fox strategy entailed the acquisition of a collection of modularized[10], best of breed, highly-advanced devices, each of which solved parts of problems and in combination formed a system capable of solving a particular problem. Hardware, software, and way of thinking about knowledge, problems, questions, and answers could be quickly re-configured as better technologies came along or needs changed – a critical capability given the ferment of Internet technologies and applications. This approach limited the amount of hardwa
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal


