NMAP Scan: Features and Applications
| ✅ Paper Type: Free Essay | ✅ Subject: Computer Science |
| ✅ Wordcount: 1558 words | ✅ Published: 23 Sep 2019 |
 NMAP Scan
NMAP Scan
Introduction:
Before we tend to start with the technical intricacies of mastering Nmap, it is a sensible
idea to know however Nmap itself began and evolved as a project. This tool has
been around for nearly twenty years, and could be a well-loved and often-used element
across several technical industries.
Nmap started from humble beginnings. in contrast to the industrial security tools that are discharged these days, the terribly 1st Nmap was solely concerning two,000 lines of code and was discharged in 1997 in issue fifty-one of Phrack, a hacker “zine” that was started in 1985. Nmap s timeline is a fascinating one, and its growth has been extraordinary.
Features of Nmap:
Although port scanning is clearly vital for security professionals—after all while not understanding what network ports are open, it’d be not possible to assess the protection of a system. Nmap is additionally terribly valuable for different styles of information technology professionals.
System directors use Nmap to work out that of their systems are on-line, so they will perceive if there are issues or inconsistencies on their network. Likewise, victimisation OS detection and repair detection, these directors are ready to easily verify that each one system are running the identical (hopefully current) versions of operating systems and network-enabled software package.
Because of its ability to alter temporal order, in addition as set specific flags on completely different packets (for example, the feast day Tree scan), developers will communicate Nmap for facilitate in testing embedded network stacks, so as to verify that the aggressive network traffic will not have accidental outcomes that will crash a system.
Lastly and maybe most importantly students of network and pc engineering are major users of Nmap. as a result of it’s a free and open supply software package, there is no barrier to induce the software package and run it in real time. Even amateur users scanning their own little home networks will learn Associate in Nursing Brobdingnagian quantity concerning however their computers and networks work and are designed by seeing what services are online though there are Windows and OS X ports, Nmap is additionally a good introduction to running easy (but advanced) tools on the UNIX system program line.
Techniques used by Nmap:
In Gregorian calendar month 2006, one among the foremost vital aspects of the Nmap project was integrated into all Nmap builds: Nmap Scripting Engine (NSE). The NSE allows users of Nmap to put in writing their own modules (in a artificial language called Lua) to trigger on sure ports being open, or sure services—or even specific versions of services—found listening. This unharness permits the elevation of Nmap from an easy networking tool to a totally strong and customizable vulnerability assessment engine, appropriate for a good type of tasks.
In addition to making a robust scanning tool and also the NSE, Nmap developers have included many further tools—including Ncrack, Nping, Ncat, and Ndiff—into default install bundles of Nmap. These tools will facilitate analyze existing scans, pivot to other hosts, transfer files, or compare scan results over time.
In this chapter, we are going to cowl the subsequent topics:
- assaultive services with Ncrack
- Host detection with Nping
- File transfers and backdoors with Ncat
- scrutiny Nmap results with Ndiff
Experimental setup and usage of Nmap:
File transfers and backdoors with Ncat
For those that might not be acquainted, an exquisite network administration tool was unveiled in 1995; it had been referred to as Netcat. This had a spread of uses, from file transfers, to network observance, to talk servers—even therefore useful on produce a backdoor by mirroring its input to a given network address of the user’s alternative. Netcat was in many ways a awfully light-weight port scanner—by employing a fast shell script, it was extremely straightforward to test whether or not sure ports were responding on a given host.
Netcat remains in significant use these days, however the Nmap development team saw some pretty serious improvements both in stability and usability that they’ll create to the software. As such, in 2009, Ncat was discharged as an element of the Nmap suite.
Unlike Netcat, Ncat has SSL support (natively), nice affiliation redirection reliability {and several and several different and several other} other inbuilt options that create it a good tool in a very security administrator s tool case.
Ncat has 2 modes: the “listen” mode, that listens on a provided port for incoming connections, and also the “connect” mode, through that commands are sent, and feedback is received. within the connect mode, we will use Ncat to attach to a variety of services, together with HTTP-based internet servers.
Sending the GET / HTTP/1.0 request when invoking Ncat via ncat nmap.org 80 yields the subsequent output:
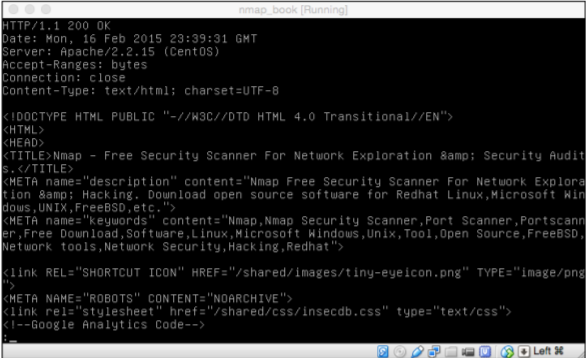
Although it clearly does not render in addition as an internet browser like Chrome or Firefox
would you’ll be able to see the HTTP/HTML response from the net server quite clearly?
This same practicality of Ncat may be wont to connect with many alternative varieties of services, together with SMTP, FTP, POP3, and so on. once trying to send completely different inputs to completely different protocols, Ncat may be invaluable!
Ncat is additionally terribly helpful once conducting a penetration take a look at or security assessment, as it may be used as each a way for information exfiltration, and as the simplest way to possess a persistent backdoor into a compromised system.
The ability to send a file through Ncat uses each the “listen” and “connect” functionalities of the tool. the subsequent screenshot shows a awfully basic Ncat command:
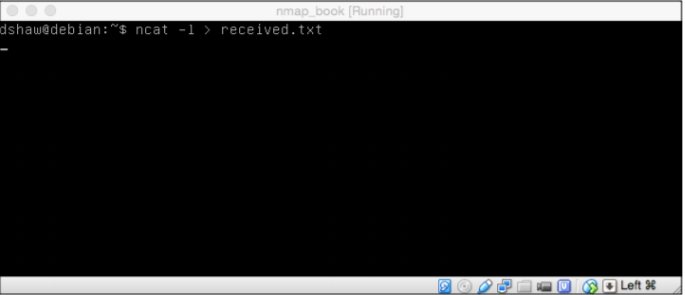
To begin, we tend to founded Associate in Nursing Ncat hearer victimisation the -l or listen flag. Since we tend to are expecting a file, we will pipe the output to received.txt. we tend to perpetually wish to form sure that we tend to are outputting the kind of file that we’re expecting so we do not have to handle dynamical file varieties at a later date. once putting in place the hearer, we can also founded a selected port (which is helpful on penetration tests); however during this case, we left the default port of 31337 intact.
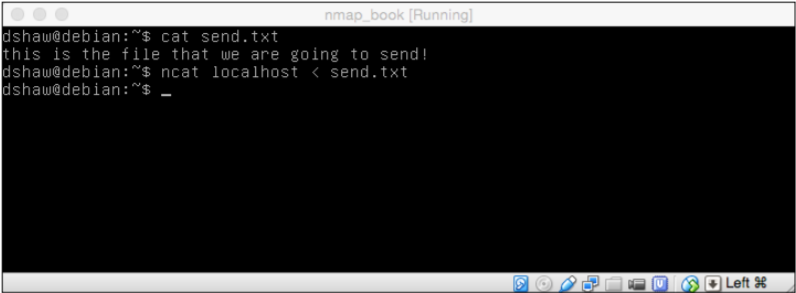
We can see within the preceding screenshot that someplace else (not within the listener) we tend to have a file referred to as send.txt with the this is often the file that we tend to are visiting send content. causation the file is easy! All we want to try to to is invoke Ncat, point it at a localhost (again, we’re victimisation the default port of 31337 therefore no port specification is necessary), and pipe the input from send.txt. the subsequent screenshot demonstrates gap a received text file:
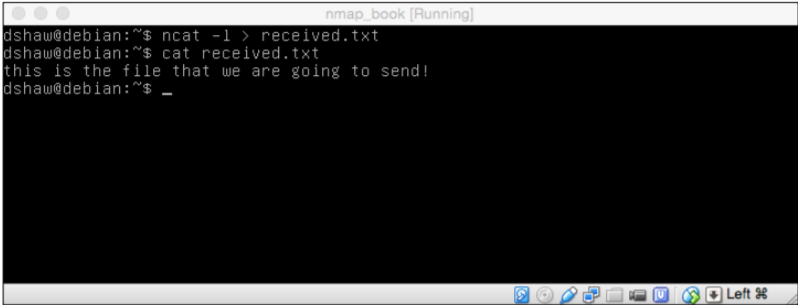
As we will see within the preceding screenshot, Ncat can mechanically shut out once the file is received. Once we tend to truly receive the file, it’s as straightforward as “cat”-in the file we tend to receive to determine that it’s after all the identical content because the one we tend to send. Lastly Ncat may be used as a backdoor, so as to make persistent access to a compromised system. the subsequent screenshot shows this basic functionality:
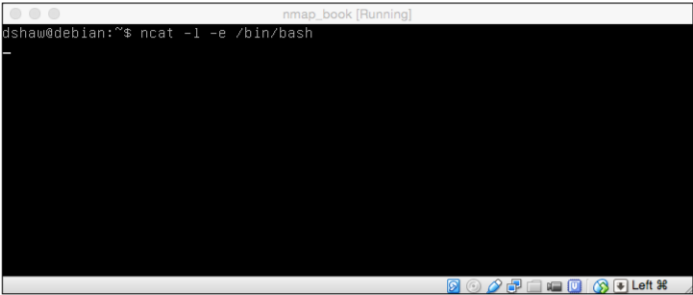
As seen within the preceding screenshot, establishing a shell affiliation via Ncat is very straightforward. we tend to used ncat -l -e /bin/bash to pay attention on the default, and dead bin/bash (our shell) once a shopper connected. It’s value noting that during this type, the backdoor isn’t persistent—meaning that it’ll not keep listening when the client has disconnected. the subsequent screenshot demonstrates the flexibility to run Linux commands on a distant system through Ncat:
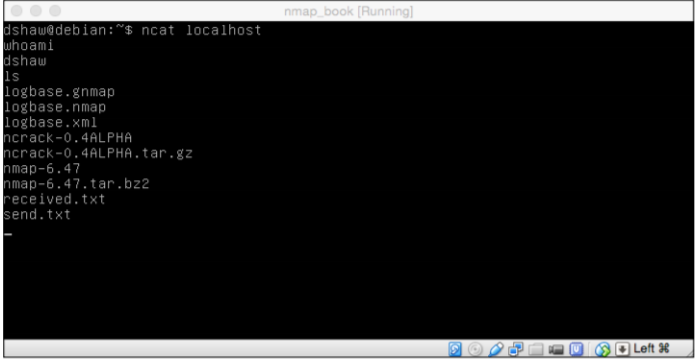
In order to attach to the shell, as shown within the preceding screenshot, we will merely invoke ncat localhost (since the port remains default) and have a bash shell spawn our prompt. during this case, we tend to run whoa mi and received back ds haw, then dead a ls command and received a directory listing of the remote directory. whereas different backdoor access ways is also a lot of reliable or difficult, it’s exhausting to suppose of one a lot of simple!
Conclusion:
Nmap may be a terribly powerful tool and it’s ability to hide the terribly initial aspects of penetration testing, that embody military operation and enumeration. this text was written in a shot to debate Nmap from the beginner level to the advanced level. There are such a big number of alternative things that you just will do with the Nmap, and that we can discuss them within the future articles.
References:
- Bagyalakshmi, Rajkumar, Arunkumar, Easwaran, Narasimhan, Elamaran, . . . Ramirez-Gonzalez. (2018). Network Vulnerability Analysis on Brain Signal/Image Databases Using Nmap and Wireshark Tools. Access, IEEE, 6, 57144-57151.
- Kalsi, T. (2017). Nmap: Network security scans. Linux Format, (219), 76-77.
- Kaur, Gurline, & Kaur, Navjot. (2017). Penetration Testing – Reconnaissance with NMAP Tool. International Journal of Advanced Research in Computer Science, 8(3), International Journal of Advanced Research in Computer Science, Mar 2017, Vol.8(3).
- Li, Hui, Kayhanian, Masoud, & Harvey, John T. (2013). Comparative field permeability measurement of permeable pavements using ASTM C1701 and NCAT permeameter methods. Journal of Environmental Management, 118, 144-152.
- Rashid, F. (2015). Nmap 7 brings faster scanning and improved IPv6 support. InfoWorld.com, InfoWorld.com, Nov 23, 2015.
- Shaw, D., & Safari, an O’Reilly Media Company. (2015). Nmap Essentials (1st ed., Community experience distilled).
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal


