A Review: IOT based Smart Home
| ✅ Paper Type: Free Essay | ✅ Subject: Information Technology |
| ✅ Wordcount: 2306 words | ✅ Published: 23 Sep 2019 |
A Review: IOT based Smart Home
Abstract– In recent years, there has been a huge development in the world of intelligent objects for home needs. Such gadgets are implements in order to ease the interaction between people and daily home duties. Although, individually simple to work with, each appliance has its own interface which adds overhead to the general user experience. This paper presents the architecture of Internet of Things. Smart homes are those where household devices can be monitored and controlled remotely. When these household devices in homes connect with the internet things using proper network, the whole system can be called as Smart Home in Internet of Things environment. This paper proposed an advanced Internet of Thing based Security Alert System for Smart Home in order to detect a motion or any unusual event at home when nobody is available there.
Keywords– Internet of Things (loT), Smart Home, Information and Communication Technologies (ICT).
N
- INTRODUCTION
owadays, around two billion individuals across the globe utilize the Internet for education sector, business, entertainment, news, information and so on, while more individuals will access such a worldwide data and identified with the utilization of the internet as a worldwide stage for letting intelligent devices impart, dialog, process and organize. It is unsurprising that, within the following decade, the Internet will exist as a consistent framework of systems and organized things. In such a traditional idea of the Internet as a framework system connecting with end-clients’ terminals is fading, leaving space to a thought of interconnected “smart” objects forming pervasive computing environments.
Smart homes constitute an important branch of computing that includes bringing safety into home appliances, wellbeing, and security. Remote monitoring frameworks are segments of intelligent homes, which use telecommunication and web innovations to control home remotely and help the household who are away from their caregivers. Home automation network provides a communication for electronic devices that are connected to sensors and switches via a central hub or a gateway. Earlier concept of homes devices can be seen as automatic garage doors, timers and many other remote control devices. But, technology advancements of present era have brought sensor networks integrated with many or almost all electronic devices being controlled through some application on a smartphone or through web.
A home needs three most important to make it intelligent, i.e., an internet network through wired or wireless, an intelligent gateway to manage sensors and system or home automation in general with a link to devices home and external services. Figure 1 shows some of major concerned areas and focuses that motivate to smart homes. Three of the services are household comforts, household healthcare and also patient security. One of the main objectives of smart homes, i.e., household comfort can be achieved by mainly two things. First is human activity identification and event automation and the second one is remote access and control of different areas of home. One of the major objective i.e. patient healthcare can be obtained by intelligent indoor local or remote monitoring.
- RELATED WORK
Wei-Chung Teng et al presents survey of a few remote sensors, which are utilized for home checking especially to care for matured individuals. The checking framework is built up on the blend of a few sensors, and it has the capacity of television information by means of remote correspondence. The focal processor gathers information and stores all information for current necessity and for future reason. The framework stores the propensity for way of life of a man.
Gowthami.T1, Dr. Adilinemacriga focuses on the monitoring and control of smart home remotely and providing security, when the user is away from the place. The personal computer is used to monitor the various parameters in the proposed system. In this system android phone is used to monitor and control the various parameters. Android phone is main advantage compared to personal computer for using any place. To monitor the various parameter using zigbee, that has viewed by lab view and then controlledusing android phone.
Patru et al presents a solution for connecting more devices into a signal entity which can be easily accessed at any time. The implementation integrates the functionalities of different home automation devices into a single application. The author described how to obtain a smart home project which integrates the functionalities of two intelligent appliances, Philips Hue light bulb and Nest Thermostat, and also several types of sensors, buzzers and motors. This system can be controlled from a mobile device with Internet access.
Ravi Kishore Kodali et al [7] describes about the implementation and deployment of wireless control system and accessibility in to a home environment for authenticated people only. A wireless network technique ZigBee based and image processing technique PCA based dedicatedly make the security system alive as per the request. ZigBee module and electromagnetic door lock module combinedly operate the door accessibility, has been designed and developed. Face detection and recognition algorithms, as well as a wireless interface are used to detect and identify visitors and send an email and/or an alert message about the current home environment status via GSM network automatically to the home owner’s mobile phone or any communication devices.
- EXISTING METHODOLOGY
Home automation and security system which can remotely control the home appliancesand alert owner on presence of intruder and occurrence of fire at home. This includes motion detection and intruderdetection in sensor circuit and LDR (light dependent resistor) and RF were exchanged. the motion detection sensor does not work properly under all situations. The alert system used in this approach is cost effective. Hence a smart home security system has to design with efficient sensor and also in low cost home Automation and Security System based on Arduino implies that whenever a person will enter the house then the count of number of the members will get incremented, bulb will start glowing and alarm will start ringing. The count of the number of household members present in the room will be displayed on the LCD screen. Whenever the room gets empty i.e. the count of the household persons reduces to zero then the bulb will automatically stop glowing making the system power efficient. Home Security System based on GSM and Android application implies that whenever a person tries to enter into the house then a SMS will be sent to household owner’s mobile phone indicating the presence of some person inside the house and the household owner can take some preventive measure in order to protect his house from the burglar. Moreover the members can control the home appliances using an android application present in the mobile phone which will reduce the individual hard work
- PROPOSED METHODOLOGY
Architecture is presented to provide security for home and some restricted places like army area, government as well as private places etc. Also, theowner/administrator can get an email alert, contains theimages of their house, regarding the theft.From the proposed hardware module, any immediatedecision can be taken as on when required (duringoccurrence of theft at home).We have tested the performance of proposed hardwaremodule over other existing approaches. for hardware implementation, we utilize the Raspberry PI3 Model B as overall system computation device. Complete working hardware module of the proposed approach. PIR sensors and security camera are connected with Raspberry PI which automatically sends signals to Raspberry PI when intrusion detected. Architecture and its research motivation; followed by a very similar product of modern world, i.e., intelligent e-meters. This paper is discussed about how researchers are focusing to find out the solutions related to security
Advantages
a) PIR sensor also works in darkness, so we get more security instead of just using camera for detection.
b) It is best cost effective, secured and suitable option for home automation.
c) The system which is implemented was a low cost and flexible that can be expanded and scaled up.
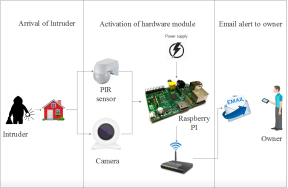
Figure1.Main architecture of proposed approach
System Implementation uses the structure created during architectural design and the results of system analysis to construct system elements that meet the stakeholder requirements and system requirements developed in the early life cycle phases. These system elements are then integrated to form intermediate aggregates and finally the complete system-of-interest (SoI). Implementation is the process that actually yields the lowest-level system elements in the system hierarchy (system breakdown structure) Raspberry PI in proposed approach as main computational device. It performs signal fetching and processing, and email sending processes. It fetches the signal from webcams and PIR sensors and send capture images to Home owner via email services

Figure 2. Hardware Module of Proposed System
- COMPONENT DESCRIPTION
For hardware implementation, we utilize the Raspberry PI 3 Model B as overall system computation device. Complete working hardware module of the proposed approach is shown in Figure 4. PIR sensors and security camera are connected with Raspberry PI which automatically send signals to Raspberry PI when intrusion detected.
Raspberry Pi
The Raspberry Pi is a series of small single-board computers developed in the United Kingdom by the Raspberry Pi Foundation to promote the teaching of basic computer science in developing countries. The original model became far more popular than anticipated, selling outside of its target for uses such as robotics. Input output devices (including keyboards, mice and cases) are not included with the Raspberry Pi. Some accessories are however have been included in many official and unofficial groups. According to the Raspberry Pi types over 5 million Raspberry Pi have been sold before February 2015, making it the best-selling British computer. By November 2016 they had sold 11 million units, and also reaching 12.5m with in March 2017, making it the third best-selling “personal computer” ever. In July 2017 it was made as an announcement that the total sales have now reached nearly to 15 million units.
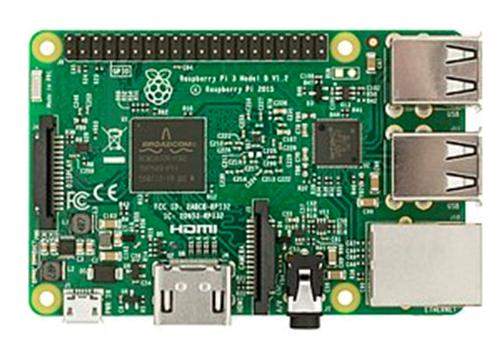
Figure 3. Raspberry Pi 3 Model B
Webcam
A webcam is a device video camera that feeds or streams its image in real time or through a system to a system network When “captured” by the computer, the video stream may be saved, viewed or sent on to other networks via systems such as the internet, and emailed as an attachment. On sending to a remote location, the video stream is saved or viewed. Similar to an IP camera (that connects using Ethernet or Wi-Fi), a webcam is normally connected using a USB cable, or a similar cable, or built into computer hardware. The term “webcam” (is a clipped compound) that is used in its original version of a video camera connected to the Web continuously for an indefinite time, rather than for a particular session, generally supplying a view for anyone who visits its web page through the Internet. Some as an example, are used as online traffic cameras, that are expensive, rugged professional video cameras.
Figure 4 Webcam
PIR SENSOR (Passive Infrared Sensor)
PIR sensor is used in proposed approach that frequently utilized as a part of movement detectors by measuring infrared lights which is transmitting from the object over sensor range. For home security, PIR is used for motion detection in home. PIR sensor also works in darkness, so user can get more security instead of just using camera for detection.

Figure 5 PIR Sensor
- CONCLUSION
The current research is investigating the concept of smart city and related factors, which have enormous impact in our daily life, with an emphasis on improving its framework’s ability to provide customized IoT functionalities. In this survey, we have presented some of the most advanced and trending researches in the fields of smart IoT based products that are ultimately shaping smart cities. The chapter covered five distinct areas in development of a smart city. We started with highlighting the improvements in smart grids’ architecture and its research motivation; followed by a very similar product of modern world, i.e., intelligent e-meters. We have discussed about how researchers are focusing to find out the solutions related to security threats in these smart e-meters. At that point, we examined the most intriguing advancements in smart homes and also illustrated research gaps in them more over. we presented some critical features of surveillance cameras and traffic control systems. Finally, we discussed overall challenges, research directions and opportunities in developing smart Home,
Future Enhancement:
The proposed system presents the basic level of home security and remote monitoring while the required objectives of home security system have been achieved. However every system has some improvement for better result. This low-cost home security system gives minimum delay during the process of email alertness. In future, fog computing has to applied to the proposed system in order to minimize the propagation delay and to enhance the security level of smart home.
References:
[1]. Aazam, M., Khan, I., Alsaffar, A. A., & Huh, E.-N. (2014). Cloud of things: IntegratingInternet of things and cloud computing and the issues involved. In Proceedings of 2014 11thInternational Bhurban Conference on Applied Sciences & Technology (IBCAST) Islamabad,Pakistan, 14th–18th January, 2014 (pp. 414–419). IEEE.
[2]. Alam, M. R., Reaz, M. B. I., & Ali, M. A. M. (2012). A review of smart homes—Past,present, and future. IEEE Transactions on Systems, Man, and Cybernetics, Part C
(Applications and Reviews), 42, 1190–1203.
[3]. Aldrich, F. K. (2003). Smart homes: Past, present and future. In Inside the smart home(pp. 17–39). Berlin: Springer.
[4]. Nishanthini, S., M. Abinaya, and S. Malathi. “Smart Video Surveillance system and alert with image capturing using android smart phones.” In Circuit, Power and
Computing Technologies (ICCPCT), 2014 International Conference on, pp. 1714-1722. IEEE, 2014.
[5]. Kim, Jung Tae. “Analyses of secure authentication scheme for smart home system based on internet on things.” In Applied System Innovation (ICASI),
2017 International Conference on, pp. 335-336. IEEE, 2017.
[6]. R. Weber, Accountability in the Internet of things, Comput. Law Secur. Rev. 27(2011) 133–138.
[7]. BUTLER Project. <http://www.iot-butler.eu>.
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal


