Anti-collision Protocols for Radio Frequency Identification (RFID) and Related Applications
| ✅ Paper Type: Free Essay | ✅ Subject: Engineering |
| ✅ Wordcount: 4450 words | ✅ Published: 18 May 2020 |
Analysis and Comparison of anti-collision protocols for Radio Frequency Identification (RFID) and related applications

Introduction
RFID stands for radio frequency identification and would correspond to a technologywhere the data is associated with RFID tags which are a type of advanced and intelligent labels input with the help of radio waves. Here the data once obtained are stored within a database which would help to identify the objects with RFID attached quite easy at a later time. When analysing the technology, RFID is a type of Automatic Identification and Data Capture (AIDC). Here one of the main advantages is that the process of identification and then later data entry into a particular database be automated to a great extent that it requires very minimal monitoring and feedback from a user. Moreover, RFID has very low energy input required, it incurs low cost to setup and also it can easily be implemented in almost in any terrain. In addition to this, one of the key elements that would make RFID is its ability to identify objects wirelessly without line of sight which have made it an optimal tool for applications in retail, stock control and deliver chain control.
However, when we are to clearly analyse the working of an RFID system quite often collisions might occur when for a single communication request that is sent simultaneous responses happen at the receiver side. As a result of data collision there can arise many problems which would primarily involve wastage of many of the resources which are critical to the functioning of the entire system. And also, this would subsequently affect the system throughput, and later lead to decreased efficiency (decreased bandwidth and increased delays) with no or less useful output obtained. To eliminate any such case of collisions that might occur during the transmission process, anti-collision protocols will have to be introduced which are essential to bring out an efficient, stable and reliable RFID system.
Primarily, An RFID system would constitute of a reader and a tag. The reader is an equipment that would pick up tags and has sufficient memory and power requirement for the same functionality. The tags are primarily of three different types active, semi active and passive tags. In general, the passive tags are durable, low cost and east to setup within an environment. Data transmission through a unique channel would aid the communication between the reader and the tag.
Analysing the functioning of an RFID system it is made up of a central processor, middleware, a reader and an antenna. The central processor is chiefly associated with processing and memory, middle ware is connected to the central processing unit, and the reader with the tag are related with the help of receivers or antennas at both the ends. [1]
If the reader is to send signals at a receiver, collision can occur quite often if multiple tags are to reply to the call made by the reader, the reader would not be able to precisely identify each tag separately which would ultimately lead to collision. This collision can be avoided by employing anti-collision protocols. A protocol is a set of procedures which is effectuated while transmitting data between electronic devices which are based on predefined set of agreements essentially defining how the transmission would occur between the sender and the receiver. Many of the protocols which are involved with data collision would constitute of Frequency division multiple access (FDMA), time division multiple access (TDMA), code division multiple access (CDMA). FDMA would assist many different users to transmit data through an independent communication channel by dividing the bandwidth of the channel into distinct non overlapping frequency sub channels where each user is granted with an independent subchannel. An example would be the coaxial cable.
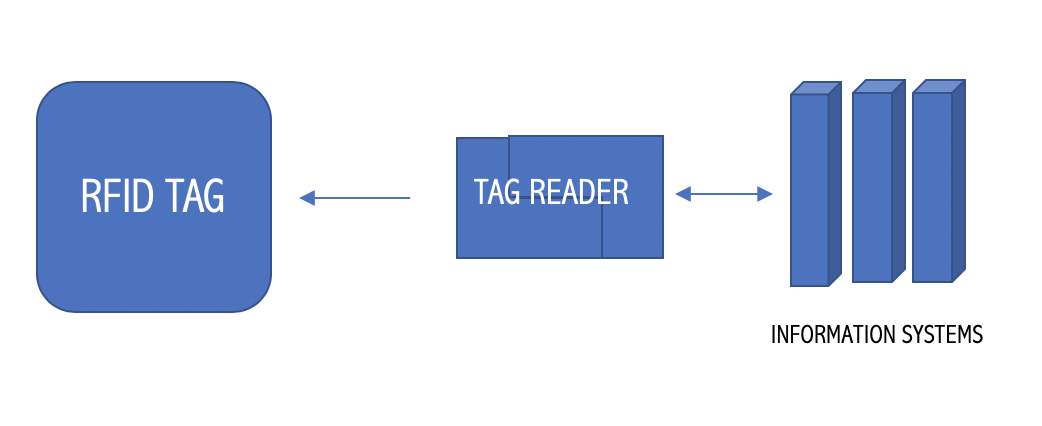
Figure 1. The RFID setup
CDMA or code division multiple access is an access method which is quite commonly used by radio related setup. Here many different transmitters can send information through one single channel. This would allow the users to exist in a band of frequencies. It’s commonly used in many different mobile phone standards including GSM, 3G and many more. CDMA involves modulation and here a local code would be executed at a very higher speed than the data that’s intended for transmission. In CDMA the bandwidth of the data is uniformly distributed over the identical transmitted power.
Again, TDMA or Time Division Multiple access is a channel access method which would allow many different users to utilise a single frequency channel by separating the signal into various time slots. Here one of the main advantages is that interrupted transmissions would happen which would result in a simple handoff. In addition to it, the slots can be allocated on demand. Within the system it involves multiple systems to utilise a single transmission medium which can be a radio frequency channel making use of only a part of the channel capacity. Many of the applications of TDMA would include GSM or the Global System for Mobile Communications and Cordless telecommunications. When compared to CDMA one of the main benefits with TDMA is that the power control is simplified due to interference. On the other hand, TDMA incurs more synchronisation overhead when compared to CDMA. [2]

Figure 2. What leads to collision
The Aloha protocol is a type of TDMA implementation where once a reader dispatches a communication request, response occurs from a tag which leads to the data being send along the transmission line. In ALOHA the sender would initiate sending a frame whenever a frame is available to send. There occurs a kind of acknowledgement whenever the frame reaches the destination. And once it reaches the destination quite successfully the next frame is transmitted. If there occurs no acknowledgment or if the frame does not reach the destination, there happens a waiting for a certain period of time and again a new frame is transmitted. In Aloha, there can occur collisions once the complexity of the network rises as there occurs a shared or common path for different sources to reach the destination. As a result of collision important data will not be transmitted appropriately and the this can lead to loss of frames and essential information. If continuous collisions are to happen on a regular basis, this can cause degradation and lower the system efficiency to a great extent.[3]
However, Another variation of ALOHA called as the slotted ALOHA would only transmit frames at regular intervals and this would drastically improve the efficiency as a whole as it would send frames only at required intervals which would make sure that there exists essential gap between the frames and thus producing less chance for collisions to occur.

Figure 3. The slotted Aloha protocol.
Another protocol that is worth considering would be the Tree protocol. The tree protocol would create a loop independent logical topology. Here there involves an inclusion of fault tolerance to be provided by the backup links if an active link would get damaged. It is based on an ID number which would be assigned to a particular tag to form a search protocol. Certain directives would determine the connection between the reader and the tag. The Tree protocol can further consist of Tree Splitting protocol, Binary Search protocol and Query Tree protocol.
Binary search protocol is a type of protocol which would not depend on the memory dependent on the ID of the tag. Here the collision bits can be identified by the reader.
Query tree protocol is based on an inquiry tree which is again not dependent on the memory.
Related Works
Luara Arjona and etal on “Energy Aware RFID Anti-Collision Protocol” found that the growing interest in networking and communications have led to the creation of transforming and identification and recognition methods. Cellular and battery-powered Radio Frequency identification (RFID) readers, inclusive of hand readers and phones have become increasingly appealing among the users mostly because they are portable and thus very convenient to use. These RFID readers require power-efficient anti-collision protocols to reduce the tag collisions and to improve the reader’s battery life. Moreover, there is an increasing interest in RFID sensor networks with a developing number of RFID sensor tags. Accordingly, RFID utility builders should have in mind of tag anti-collision protocols.
Green electricity implemented protocols contain a low reader energy intake consistent with tag. This gives a thorough observation of the reader power intake along with tag and analyses the primary thing that affects this metric: the frame size update method.
Using the belief of this analysis, the anti-collision protocol Energy-Aware Slotted Aloha (EASA) is presented to lower the strength intake in line with tag. The frame size update approach of EASA is configured to minimize the electricity consumption per tag. As a result, EASA offers an energy-aware body. The overall performance of the proposed protocol is evaluated and compared with several of the Aloha-based anti-collision protocols based totally at the contemporary RFID preferred. Simulation results disp lay that EASA, with an average of 15 mJ consumed up in line with tag recognized, achieves a six percent average improvement in the power intake per tag when it comes to the techniques of the evaluation. [6]
Xiaolin Jia and etal on “Analysis of Anti-Collision Protocols for RFID Tag Identification” explains that the Radio frequency identity (RFID) systems are becoming ubiquitous. Simultaneous transmissions in RFID structures lead to collisions as the readers and tags normally function on the same channel. Consequently, anti-collision protocol may be very essential for fixing the collision hassle in RFID application machine.
Radio frequency identification (RFID) generation is an automated identity method, relying on storing and remotely retrieving data with devices known as RFID tags and readers. RFID structures encompass digital tags connected to physical objects, readers sensing the tags, and middleware that procedures the RFID information in response to request from RFID packages.
The RFID programs are several and a way reaching. The maximum exciting and successful programs consist of the ones to deliver chain control, production system control, gadgets tracking management. Many programs of RFID, which include container terminal and massive Warehouse, need to discover more than one tags once a time. Since RFID readers and tags speak via a wireless channel, simultaneous transmissions in RFID structures lead to collisions as the readers and tags generally perform at the same channel. Consequently, powerful and efficient anti-collision protocols are very critical for RFID programs, which are required to identify objects attached with tags concurrently. Many anti-collision protocols for RFID tag identification have been proposed at present. Collisions in a RFID machine or a typical RFID system is specially composed of radio frequency verbal exchange subsystem which can constitute of RFID read or write and RFID tags, and laptop records subsystem or information processing subsystem.
The utility software initiates all readers and tag activities. RFID offers a short, flexible, and reliable way to electronically stumble on, tune and manage a collection of items. RFID systems use radio transmissions to send signal to a RFID tag, even as the tag emits a completely unique identity code (identity) back to the RFID reader. If multiple tags are to be identified concurrently, collision could be happening. As a result of this, anti-collision protocols want to be devised among the tags and the reader to minimize collisions. The RFID collision troubles could be summarized and labelled into, tag-to-tag collision (or tag collision), reader-to-tag collision, and reader-to reader collision. Each reader-to-tag collision and reader-to reader collision are known as reader collision in well known. The tag-to-tag collision, takes place when a collection of the tags responds to a single reader’s inquiry simultaneously and consequently the reader cannot perceive any tag.
Reader-to-tag collision happens when one tag is concurrently located in the fields of extra readers and multiple readers try to speak with that tag on the identical time. Reader-to-reader collision occurs when a reader transmits a sign that interferes with the operation of some other reader, for that reason stopping the second reader from communicating with tags in its interrogation zone. In different words, the reader collision indicates that a plurality of reader requests inquiries to one tag simultaneously, so it’s far perplexing for the tag to identify the inquiries.[5]
Zhijun Tang and etal on “Research of Multi-access and Anti-collision protocols in RFID systems” discusses that due to the limitless possibilities and low cost, Radio Frequency identification (RFID) structures have been considered as a low-cost solution for object identity. They are a cheap and error control resource to conventional object identity strategies. Simultaneous transmissions in RFID structures result in collisions as the readers and tags usually perform in a shared wi-fi channel. Consequently, collision arbitration for RFID tags and readers is an enormous difficulty for instant identification.
Radio frequency identity (RFID) structures have acquired a whole lot attention in many industries, manufacturing companies, material go with the flow structures, and many others. An incorporated RFID system is composed of four different primary additives, wherein the readers try to pick out the tags as fast as possible through wi-fi communications. The collision trouble occurs in signa. transmission of the readers or the tags, which hardly ends in rapid identification. Consequently, it’s far a key problem to be considered as a secure anti-collision protocol with a purpose to lessen collisions. RFID collision issues may be summarized with the help of tags identity problem and readers collision problem.
The RFID collision issues are grouped into tag collisions and reader collisions and the tag collisions occur more frequently in RFID systems. The tag collision issues are subdivided into active tag collisions and passive tag collisions and quite often passive tag collision issues are more complex. The tag collisions arise in the case where more than one tag reflect a sign at the same time confusing the reader. Due to low-functional entities, passive tags can’t determine the neighbouring tags or they can result in collisions, thus it’s very important to expand a tag anti-collision protocol enhancing the identification capability of RFID structures. Reader collision problems are subdivided into reader-tag collision issues and reader-reader collision problems. Reader-tag collision takes place while the signal from a nearby reader interferes with tag responses being acquired at some other reader. Reader-reader collision happens when a tag hears more than one reader at the same time. In this case, the tag may not be able to respond to any reader in any respect. [9]
Feng Zhoua and etal on “Evaluating and Optimizing Power Consumption of Anti-Collision protocols for Applications in RFID systems” suggests that in general for RFID systems, the layout of passive tags is a key difficulty in anti-collision protocols wherein fall in electricity intake permits a longer operating distance among tags and the reader.
An improved protocol is also provided for power intake savings. Radio-Frequency identity (RFID) systems encompass radio frequency (RF) tags and networked electromagnetic readers. The reader tries to gain inside its study range for a specific identity variety of every tag. The requirement for imposing low-value automatic identification systems calls for passive electronic tags that get their electricity from the electromagnetic waves emitted from the reader. For frequencies above 900MHz, the working distance of 1 meter or above makes tags fall into region of the reader’s antenna. The energy obtained via the tag is usually less than one hundred microwatts. Such a power deliver requires the function of the tag to be as easy as possible in order that its strength intake may be decreased. The statistics transmission from tag to reader is performed by means of scattering the wave electricity returned to the reader. Relying on the data being despatched again to the reader which can be a zero or a one, the tag chooses to scatter or not to scatter the wave strength or as an alternative modulates the service with one-of-a-kind frequencies at the same time as scattering. A collision problem might also get up while a couple of tags enter the running sector of a reader. In reaction to the reader’s inquiry, every tag sends a sequence of records to the reader. The reader will get hold of a mixture of scattered waves and cannot inform about the existence of Individual IDs of the tags.
Due to such an issue, an anti-collision mechanism is wanted in such an RFID device and must be applied within the digital circuits present in the tags. The power supply for tags makes it impossible to set up the communication that a number of the tags might require to coordinate their scattering behaviours. As a result of this, the anti-collision scheme must be in the mode of “reader-inquiring” and “tag answering”. The manner of inquiring and answering is repeated for some of cycles until the process of getting access to all the tags is done. A passive tag is limited of its activity due to the amount of its power intake when compared to energy-constrained. It can be well expected that the reader always continues the supply power and such that at some stage in the in order that the concern of “battery existence” would no longer be present. The main problem would be the tag’s electricity consumption, which would limit the maximum working distance between the tags and the reader. As the anti-collision circuit constitutes of a part of the base-band processing unit on a tag, low electricity implementation of anti-collision protocols guarantees to be important inside the layout.
In a passive RFID machine, no anti-collision protocols may be evaluated appropriately in terms of electricity intake without a particular implementation. This is primarily due to the reason that the limit on power intake has come to such a volume that each the protocol and circuit have to be optimized accordingly. [4]
Comparison of Key approaches
The above-mentioned protocols are all efficient and can be adapted to a particular setting based on their features and the other requirements. Each have its own merits and demerits. Once we are to clearly analyse the protocol and their requirements, an optimal protocol would be a one with very minimal flaws which might to lead to drop in the system performance and which would result in a higher system efficiency.
While different options are available the basic protocols like CDMA, TDMA and ALOHA can always be a preference as the anti-collision protocol to be implemented. The rate of data transmission would be higher for CDMA than TDMA. This would make it a better option in case if the setting demands faster transmission rate. In CDMA the signals are transmitted as digital signals while in TDMA, the signals occur in bursts. CDMA systems in general has higher potentiality than the TDMA systems as a whole. On the other hand, TDMA systems in general would take up very less amount of expenditure to be setup when compared to CDMA systems where although the setup cost is very high, the cost for operating the system can be less.
The procedure that’s involved in CDMA would involve sharing the bandwidth along with time. While, in TDMA it involves sharing the time of satellite transponder. Synchronisation is needed in the case of TDMA, while there is no synchronisation requirement in the case of CDMA. Both CDMA and TDMA are equally efficient once the power consumption is considered. There occurs a case of frequency hopping in CDMA as result of which the performance would significantly get affected as a result of adjacent time and frequency slots. However, one of the major disadvantages with CDMA is that there can arise the near far problem. The VTR or the variable transmission rate can be quite easily be setup in the case of both CDMA and TDMA. [8]
Again, the comparison can be made between the above given protocols can be based on many other features like Usage, the type of method implemented, based on channel utilization and many other parameters.
While comparing tree and Aloha dependent algorithms, it can be inferred that within the tree protocol method the operation is primarily by assembling the replying tags into many different subsets and then recognising and reading the tags in each of the subset in a sequential order. While within the Aloha based protocols, the tags will have to respond asynchronously or with synchronized slots or frames. The Aloha protocol is primarily based on probabilistic method while Tree protocol can be based on deterministic method. There occurs Tag starvation in the case of Aloha protocols, while no such event is seen in the case of Tree protocol. There occurs a forty percent channel utilisation in the case of tree protocols, while for pure Aloha the channel utilisation can be comparatively be less which can be around sixteen percent. One of the main advantages within the ALOHA protocol is that it requires no synchronisation between the users for it to operate efficiently. However, it has very low throughput when put under heavy load. The collision event can also happen more often when the number of users would be more. One of the major advantages using the tree protocol would be that the number of tags to reader commands would be significantly be higher than other protocols. This would make it easy to configure it to any setting as the commands can be implemented accordingly. [11]
Within the tree protocols the Query tree, Tree splitting method and the Binary search method all have their own characteristic method. In the query tree method, the reader would send a query initially and tags with the matching prefix would respond. While within the Tree splitting method there can happen collision resolution as the colliding tags are separated into different disjoint subsets. In both of the methods, the time complexity would be around Big-Oh(n) and they are equally efficient.
When comparing pure Aloha and the slotted Aloha methods for transmission, it can be found that within the pure Aloha method a tag would send it’s ID to the reader after a certain time. If a collision is to happen, the tag would transmit again after certain delay. While with slotted aloha, it involves synchronised slots where the tags are associated with these slots for transmission. If a collision occurs, the response from the tag would occur after a certain number of slots. Within Pure Aloha method it would require a timer, while within slotted Aloha it needs timer and synchronisation circuits. Slotted Aloha would have comparatively higher throughput than pure Aloha where the former has a throughput of around 37 percent while the latter has a throughput of 17 percent. Slotted Aloha is undeniably a better method as it can minimise collision occurrence as well because the data is transmitted at regular intervals. One of the major downsides of pure Aloha is that along with the increase in the load, the collision probability would also rise which would gradually result in increased number of collisions. This is the same with slotted as well. In addition to this, within slotted aloha it might also require synchronisation to occur between the reader and the tag. Slotted Aloha is more expensive to setup than pure Aloha. [7]
The tree-based protocol would detect the tags which are present in the interrogation zone. The reader would control the protocol procedure throughout with the help of commands to produce subsets from the tags undergoing collisions. And the subsets are also divided again until all of the tags are recognised. While within Aloha protocol it can be observed that random multi access would refer to recognising more tags. While implementing, the tree protocols are mainly put in ultra-high frequency and microwave RFID systems. While the Aloha protocols are mainly setup in low frequency and high frequency RFID systems making it an optimal choice for low scale operation.
Conclusions and future directions
As a fundamental wireless object recognition technology, RFID generation is growing rapidly with increasing development of the internet of things which will later lead to an increase in the market scale. Statistics integrity, as one of the key technologies innate to RFID, will draw the eye of a big quantity of researchers. Anti-collision protocols may also seem in more in demand in such a case.
While determining the right anti-collision protocol, various factors will have to be considered including the bandwidth usage, range, power consumption, Cost of setup, power efficiency, and mode of data transfer. The optimal choice for the anti-collision protocol would be the one with higher power efficiency, an increased value of range, less delay, and would cost less expenditure to setup. The protocol implemented should also be more flexible and adaptable to any setting resulting in very minimal loss of data at any instance. The mode of data transfer would also be a factor in determining the right protocol. Most Importantly, choosing the right protocol can minimise energy loss, can result in a faster data transmission, produce greater throughput and the expected results at a much faster rate. Also, this will prevent any kind of errors that might happen during the transmission process making the system more reliable as a whole.
References
[1] Klair, D. K., Chin, K. W., & Raad, R. (2010). A survey and tutorial of RFID anti-collision protocols. IEEE Communications Surveys and Tutorials, 12(3), 400–421. https://doi.org/10.1109/SURV.2010.031810.00037
[2] Shih, D. H., Sun, P. L., Yen, D. C., & Huang, S. M. (2006). Taxonomy and survey of RFID anti-collision protocols. Computer Communications, 29(11), 2150–2166. https://doi.org/10.1016/j.comcom.2005.12.011
[3] Cmiljanic, N., Landaluce, H., & Perallos, A. (2018). A comparison of RFID anti-collision protocols for tag identification. Applied Sciences (Switzerland), 8(8). https://doi.org/10.3390/app8081282
[4] Zhou, F., Chen, C., Jin, D., Huang, C., & Min, H. (2004). Evaluating and Optimizing Power Consumption of Anti-Collision Protocols for Applications in RFID Systems. Proceedings of the International Symposium on Low Power Electronics and Design, 2004–January(January), 357–362. https://doi.org/10.1109/LPE.2004.241227
[5] Jia, X., Feng, Q., Fan, T., & Lei, Q. (2012). Analysis of anti-collision protocols for RFID tag identification. 2012 2nd International Conference on Consumer Electronics, Communications and Networks, CECNet 2012 – Proceedings, 877–880. https://doi.org/10.1109/CECNet.2012.6202109
[6] Arjona, L., Simon, H. L., & Ruiz, A. P. (2018). Energy-aware RFID anti-collision protocol. Sensors (Switzerland), 18(6). https://doi.org/10.3390/s18061904
[7] Shin, W. J., & Kim, J. G. (2009). A capture-aware access control method for enhanced RFID anti-collision performance. IEEE Communications Letters, 13(5), 354–356. https://doi.org/10.1109/LCOMM.2009.081970
[8] La Porta, T. F., Maselli, G., & Petrioli, C. (2011). Anticollision protocols for single-reader RFID systems: Temporal analysis and optimization. IEEE Transactions on Mobile Computing, 10(2), 267–279. https://doi.org/10.1109/TMC.2010.58
[9] Zhijun, T., & Yigang, H. (2007). Research of multi-access and anti-collision protocols in RFID systems. 2007 IEEE International Workshop on Anti-Counterfeiting, Security, Identification, ASID, 377–380. https://doi.org/10.1109/IWASID.2007.373659
[10] Cheng, T., & Jin, L. (2007). Anti-collision Algorithms. Simulation, 697–701.
[11] Alsalih, W., Ali, K., & Hassanein, H. (2013). A power control technique for anti-collision schemes in RFID systems. Computer Networks, 57(9), 1991–2003. https://doi.org/10.1016/j.comnet.2013.03.016
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allDMCA / Removal Request
If you are the original writer of this essay and no longer wish to have your work published on UKEssays.com then please click the following link to email our support team:
Request essay removal


