Cloud Security in the Business Environment
Info: 9152 words (37 pages) Dissertation
Published: 23rd Feb 2022
Tagged: BusinessCyber Security
Abstract
With the development of Cloud Computing, Data security becomes more important in Cloud Computing. This paper gives an overview on cloud security and seeks to identify the major security issues and their solutions in cloud computing security as well as identifying areas for future research. Although many security issues and solutions were identified it has become apparent that much of the research being done only relates to the theoretical side. Therefore the paper also shows us the use of cloud security in business environment and shows the architecture of working of cloud service providers and also explores the use of cloud security which helps the business world to keep safe the data and gain more capital.
Keywords: Systematic literature review, Cloud computing Security, Virtualization, Cloud service provider
Abbreviations
CC Cloud Computing
CSP Cloud Service Provider
DOS Denial of Service
DDOS Distributed Denial of Service
HAAS Hardware as a Service
ID Identification Document
IT Information Technology
IAAS Infrastructure as a Service
LAN Local Area Network
OS Operating System
PAAS Platform as a Service
RAID Redundant Array of Independent Disks
RAM Random Access Memory
SAAS Software as a Service
SIO System Initialisation Operator
SLR Systematic Literature Review
SSL Secure Sockets Layer
TPA Third Party Auditing
TTP Trusted Third Party
VLAN Virtual Local Area Network
VM Virtual Machine
VMM Virtual Machine Monitor
Table of Contents
Click to expand Table of Contents
1.0 Introduction to Cloud Security
1.2 Problem Area in Cloud Security
1.3 Motivation
1.4 Delimitations
2.0 Literature Review About Cloud Security
2.1 History
2.2 Definitions
2.2.1 Information Security of Cloud
2.2.2 Cloud Computing
2.2.2.1 Public cloud
2.2.2.2 Private cloud
2.2.2.3 Hybrid cloud
2.2.2.4 Community Cloud
2.2.3 Service Models in Cloud Security
2.2.3.1 Infrastructure as a Service in Cloud Security
2.2.3.2 Software as a Service in Cloud Security
2.2.3.3 Platform as a Service in Cloud Security
2.2.3.4 Hardware as a Service in Cloud Security
2.3Types of Cloud Security
2.3.1 Virtualization and Multi Tenancy
2.3.2 See Cloud
2.3.3 RAID
2.4 Cloud Security Issues
2.4.1 Data Privacy and Integrity
2.4.2 Deduplication
2.4.3 Loss of Control, Backup Issues and Availability
2.5 Cloud Security solutions
2.5.1 Various Path of Solutions in Cloud Security
2.5.1.1 Security Governance, Risk Management and Compliance
2.5.1.2 People and Identity Management
2.5.1.3 Application Security
2.5.1.4 Information Security
2.5.1.5 Physical Infrastructure
2.5.2 Auditing in Cloud Security
2.5.3 Policies in Cloud Security
2.5.4 Biometrics in Cloud Security
2.5.5 Hardware as a Service in Cloud Security: Physical and virtual hardware on demand
3.0 Practical Contribution of cloud Computing and Cloud Security
3.1 Contribution in Business Environment
3.2 Application
3.3 The List of Companies Uses and Provides Cloud Security
3.4 Google Security Layers for Users
3.4.1 Continuous Delivery of Google Cloud Security.
4.0 Analysis and Discussion
5.0 Findings
6.0 Outcome
7.0 Conclusion
References
1.0 Introduction to Cloud Security
This section provides a background for the review. Thereafter a research problem is defined and a motivation for the review is presented. The section is concluded with a presentation of the delimitations and the outline of the review. Cloud computing (CC) is a network model that makes it possible to achieve on-demand network access and a shared pool of configurable resources, e.g. networks and servers, which can be provided with minimal management or interaction. Simplified, this means that CC represents a model for network access that does not require the same level of maintenance as a standard organizational network would. Clouds are so integrated in our everyday life that most people don’t even think about them being used. Examples of everyday CC are platforms such as I cloud, Office 365 and Google Drive.
It eliminates the requirement of having expensive computer hardware, software and the designated space. Massive growth has been observed in the big data which is generated with the help of cloud computing. Large computational infrastructure is required to address the big data to ensure the processing and analysis of data successfully which is quite time-demanding and challenging task. Cloud computing is considered as one of the most noteworthy shift in modern ICT for enterprise applications. It has become an effective architecture to do complex and large-scale computing (Almorsy, 2016).
1.2 Problem Area in Cloud Security
Initially it is important to mention that the reviewed subject already has a solid foundation in the shape of relevant literature. This review aims to analyse this foundation and summarise it in order to present the reader with a factual, up-to-date depiction of the current security risks and solutions within the CC field. The need for this is simple: since cloud computing continues to grow exponentially it is of utter importance to stay updated on the present risk and solutions in order to ensure that future clouds are developed based on the latest insights. The problem presents itself in the massive amount of relevant literature you would have to sift through in order to gain these aforementioned insights. It would also be hard to know which literature is trustworthy in comparison to one another. Thus, this review aims to analyse current literature within the CC field demarcated to security risks and solutions in order to form a concrete summarisation which can then be used as an overview by any other individual.
1.3 Motivation
Information security is an important feature in all sorts of systems. Security within cloud computing is no exception. In fact, one quick search on Google Scholar with the search terms “cloud computing security” will warrant roughly 67 000 results even while disregarding results from before 2011. This confirms that the area of CC security is a widely researched subject. While that in itself is an indication that security within CC is a palpable problem, the massive amount of research also contributes to the problem in the sense that finding relevant literature becomes a difficult task. As a result of this increased difficulty there seem to be a lack of summaries regarding the subject. This is proven by the fact that a perspicuous analysis of the subject cloud computing security, pertaining to both current solutions as well as risks, is non-existent based upon the authors’ own findings. As such, the purpose of this review is to analyse relevant literature within the CC area. It is essential to clarify that the review does not aim to produce an applicable solution for the aforementioned risks, but instead provide a straight forward, current depiction of security within CC. of the subject cloud computing security, pertaining to both current solutions as well as risks, is non-existent based upon the authors’ own findings. As such, the purpose of this review is to analyse relevant literature within the CC area. It is essential to clarify that the review does not aim to produce an applicable solution for the aforementioned risks, but instead provide a straightforward, current depiction of security within CC.
1.4 Delimitations
This review is oriented to the area of security within the field of CC. Security is an interesting area to examine as it is quite significant and new research is continuously being produced. At the same time, this brings certain difficulties. A decision was made to only include literature from the year 2011 and onward. The reasoning behind this is that cloud computing grows exponentially and as such new security risks are constantly identified, and solutions constantly developed. In order to ensure up to date information is used literature produced before 2011 was not deemed appropriate for this review. Due to the study’s timeframe another decision was made. As mentioned in section 1.3, this study will not aim to produce a solution for any specific security risks but instead produce a summary of existing solutions and risks.
2.0 Literature Review About Cloud Security
2.1 History
The term “cloud” is utilized for Internet and other communication system representation along with abstracting the involved underlying infrastructures. “Cloud” term was utilized to symbolize the computing space between the end user and provider. Companies started to gain improved perceptive of cloud computing and its advantages to provide outstanding services and solutions to their customers along with improving the inner efficiencies during the second half of 1990s. Salesforce.com has become one of the first key movers in cloud area in 1999 which was a revolutionary step to utilize the concept of providing enterprise level system applications to the end users through Internet. After the introduction of this novel perception to the world by Salesforce.com, Amazon.com introduced the web-based retail services in 2002. Amazon was the foremost key association which modernizes their data centres that were using only around 10% of their capacity at any specific time. It was realized by Amazon that the new concept of cloud computing model allowed them to utilize their existing capacity with more efficiency. In the meantime, Google had become the major player in the marketplace of Internet commerce. Google had launched Google Docs services in 2006 that brought the effectiveness of cloud computing and sharing of data directly with the end users (Sanaei, 2013).
2.2 Definitions
This section of definition includes the cloud security and various background of cloud computing which helps to understand more about the security issues in security.
2.2.1 Information Security of Cloud
Ensuring the confidentiality, integrity and availability, also known as the CIA triangle, has been considered the industry standard for quite some time now. While these characteristics remain of utmost importance, the rapid development surrounding the IT sector means this definition must be expanded in order to encapsulate the new security situation.
Information and communication technology (ICT) can arguably be considered a sub- component of information security since information security includes the protection of underlying resources defines ICT security as all aspects relating to defining, achieving and maintaining the confidentiality, integrity, availability, non- repudiation, accountability, authenticity and reliability of information resources. Thus, argues that a clear understanding of these additional characteristics is essential as without them, information cannot be considered secure .As such, whenever this review utilises the terms “security” or “information security”, this is the definition being referred to. (M.G.Avram, 2014)
2.2.2 Cloud Computing
Some key characteristics of CC are that it is capable of on-demand self-service as well as capable of rapid elasticity. This means that not only should a user be able to access the cloud without human interaction, in addition the cloud environment capabilities should be automatically scalable aside from this a cloud environment must also be available over the network, capable of resource pooling and capable of being measured. This means that a cloud environment must contain mechanics for monitoring, reporting and controlling the above mentioned characteristics Furthermore; clouds are deployed using different deployment methods, or types of clouds. It is important to know the difference between the different deployment methods as they can impact which security risks and solutions that are applicable to a cloud. The common ones are public, private, hybrid and community cloud. (Almorsy, 2016)
2.2.2.1 Public Cloud
The simplest way to describe a public cloud is an infrastructure that is used by the public and provided by a government, organisation or other companies (Mall & Grance, 2011).
2.2.2.2 Private Cloud
A private cloud is used exclusively by an organisation and the cloud provider is either the organisation themselves or a third party (Mall & Grance, 2011).
2.2.2.3 Hybrid Cloud
A hybrid cloud is an infrastructure that combines public and private clouds. It consists of a composition of two or more clouds that all remain unique entities but are bound together by standardised or proprietary technology (Mall & Grance, 2011).
2.2.2.4 Community Cloud
A community cloud is used by a community of consumers from various organisations that share common views. This particular setup may be controlled and maintained by a third party or by the organisations .In addition, a community cloud setup may reside inside or outside the CSP premises .Community cloud consumers therefore seek to exploit economies of scale while at the same time minimising the costs associated with private clouds or hybrid clouds as well as the risks associated with public clouds (Boampong & Wahsheh, 2012).
2.2.3 Service Models in Cloud Security
Clouds use architectural models in order to provide different services to the users. Service models are not tied to a specific deployment type, public, private, hybrid and community; rather each deployment type can use each service model.
Just as with the different deployment methods the service models can have implications for a clouds security state, it is therefore important to have knowledge of these service models. The common service models are explained below.
The figure below consist of the models which approaches to the cloud security models are defined and explained below
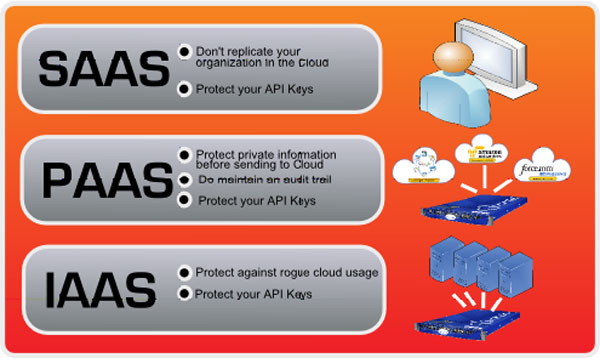
Figure 1 Service Models in Cloud Security(Li, 2012)
2.2.3.1 Infrastructure as a Service in Cloud Security
Infrastructure as a Service, often abbreviated to ‘IAAS’, consists of offering infrastructure solutions as a service. The major benefit of this is the ability to only pay for what you actually use an example of this is Drop box where the user can pay more or less depending on how much storage they need.
2.2.3.2 Software as a Service in Cloud Security
Software as a Service, often abbreviated to ‘SAAS’, utilizes an instance of an application and the underlying database to offer the software to multiple customers simultaneously.
2.2.3.3 Platform as a Service in Cloud Security
Platform as a Service, often abbreviated to ‘PAAS’, provides a platform that can be used during the development of an information system, e.g. for testing and distribution. Examples of these kinds of services are GAE and Microsoft Azure.
2.2.3.4 Hardware as a Service in Cloud Security
Hardware as a Service, often abbreviated to ‘HAAS’. It brought forth a significant improvement because it allows for easy access to physical hardware devices, distributed among several geographical locations. If the cloud consumers subscribe to this service, it will appear as if they are connected to the local machine. The HAAS cloud middleware will ensure transparency between data exchanges while the local system considers all connected hardware to be locally connected
2.3 Types of Cloud Security
2.3.1 Virtualization and Multi Tenancy
Virtualization and multi tenancy are two of the core technologies that enable CC to be used as we know it today. A traditional way of hosting applications and data storage involves running one operating system (OS) on one physical server. This traditional hosting method can also be used to create a functioning but inefficient cloud. This is achieved by linking multiple servers using a Virtual LAN (VLAN). This is secure but inefficient in the long term as a large part of the physical hardware available end up being unused. Virtualization was built in order to solve this efficiency problem. By using a Virtual Machine Monitor (VMM) a single physical server can host multiple instances of an OS. This means that a single server can utilize the available hardware power in a more efficient manner.
The figure below is a basic illustration of a VMM running multiple instances of an OS using a virtualization layer. The virtualization layer is often known as hypervisor. There are two main ways of utilizing this hypervisor to run virtual machines (VM). These are known as full virtualization and Para virtualization the difference between them lies in how much of OS needs to be emulated. A VM deployed using full virtualization has to emulate the BIOS and drives of the OS, in addition to the other functions. A VM using para virtualization runs a version of the OS that has been modified to work without needing a BIOS or similar components (Mishra et al., 2013).
There are also two major architectures used to deploy virtual machines, hosted architecture and hypervisor architecture. The difference here stems from the way the hypervisor is handled by the server. In a hosted architecture the hypervisor is a platform that the host OS runs as a normal application. The application is then charged with the upkeep of the virtual machines. On the other hand hypervisor architecture skips the OS and is instead run directly on the hardware. Depending on which deployment method and architecture used different security aspects apply (Mishra, Mathur, Jain & Singh, 2013).
Multi tenancy is closely tied to virtualization. In short, multi tenancy allows several users to share computing resources with logical separation of the different users; a user in this case is a tenant of the system (Mishra et al., 2013). In the context of cloud computing, each VM can be considered a tenant. However multi tenancy is not limited to multiple VMs running on the same hardware. Applications can also be utilised in a way that allows multiple tenants to use them, while at the same time separating the different users from each other (Mishra et al., 2013). While virtualization and multi tenancy is core technologies needed for cloud computing to remain efficient and viable they introduce new security risks
The below diagram show us the description image of virtualization of the process.
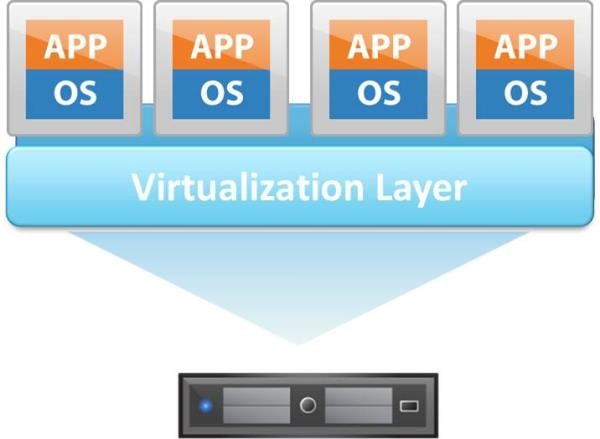
Figure2: Descriptiveimageof Virtualization(Dinh, 2011)
2.3.2 See Cloud
See Cloud is a basic protocol which uses identity based cryptography. An overview of what this actually means and how it works is followed by the steps presented below.
The System Initialisation Operator (SIO) generates system parameters as well as master secret keys. After the system parameters are set the SIO selects a random number as its master key and another one for its public key. Once a user connects to the cloud it must first be registered with the SIO. The user can do this by using its unique ID, e.g. a user ID, and is then provided a secret key by the SIO through a TLS or SSL connection before the user can upload data to the cloud, the necessary storage for it is requested and is then allocated by the CSP. In an attempt to ensure data storage auditing, the user has to sign every single transmission block in order to generate authenticate data. See Cloud has a function that allows an organisation to be set as ‘trusted’ which means the above mentioned process can be completed automatically. The data is then encapsulated and a session key is created before it is sent to the CSP. Once it’s been received, it is decrypted by using the session key and the user’s signature is verified.
After the steps mentioned above, the result is verified in order to confirm that everything has been completed in a correct manner, e.g. that the data has been stored at the correct positions. What separates Sec Cloud from other cryptographic protocols is the effectiveness, the usage of auditing at the time of uploading and that several users can be handled simultaneously through batch verification. In addition to this basic protocol, there are also other forms of the Sec Cloud protocol such as Sec Cloud+ and Sec Cloud HDFS. These are more advanced and as such, require further computing power but offer new forms of security. One of these additional types of security is deduplication of data. Sec Cloud+ also offers the possibility to encrypt the data before uploading (Wei et al., 2014).
As of today, clouds don’t generally store massive amounts of data. But from an analysis report performed by Li, Li, Xie and Cai (2015) this will not be the case in just 5years’ time. They estimate the volume of data by 2020 to be 40 trillion gigabytes. Thus, a user should demand improved security and integrity surrounding their data from the CSP.
2.3.3 RAID
In the system architecture ”Robust, Scalable and Secure Network Storage (RSSNS)” presented by Al-Anzi, Salman, Jacob & Soni (2014) an encryption mechanism is first applied to the data which in turn is split into cipher blocks. These blocks of cipher data are then placed among several different CSPs. E.g. if a customer stores a file, A, on the cloud. A is then encrypted before uploading and is split into different blocks of data; A1, A2 and A3. These are then distributed on different servers within the cloud.
RSSNS achieves this by applying a Redundant Array of Independent Disks (RAID) implementation at each server within the cloud. They compare different versions of RAID and reach the conclusion that RAID 10 (1 + 0) is most efficient. RAID 10 provides several unique features such as data redundancy, availability and fault tolerance by mixing the features of striping and mirroring. Availability is achieved by the usage of parity. Parity, in short, is information pertaining to a specific cipher block and can be used to reconstruct a file that’s been damaged or is unavailable for various purposes. E.g. if A1 is stored in S1, A2 is stored in S2 and A3 is stored in S3, the parity information from A1 and A2 is stored in S3. Thus, if A1 is damaged, the complete file can still be reconstructed using the information stored in S2 and S3 (Al-Anzi, Salman, Jacob & Soni, 2014).
2.4 Cloud Security Issues
2.4.1 Data Privacy and Integrity
Data is kept private and secure from unauthorised users as well as free from malicious or unintentional modifications is not an easy task. When managing these aspects of security one main issue is the lack of control a cloud user has over the actual server the data is stored on (Chen & Zhao, 2012).
Data stored in the cloud can be divided into two groups, IaaS environment data and data in PaaS or SaaS environments. IaaS data is data that is stored in the cloud instead of on a local hard drive; examples of this include services such as Amazon Simple Storage Service. PaaS and SaaS data differs from this since this data is primarily used in applications processing the data, not necessarily storing it long term (Chen & Zhao, 2012).
Data stored in an IaaS environment can simply be encrypted in order to decrease the risk of private data becoming public. However this is not always as easy as it sounds as the encryption will only be as secure as the encryption method chosen. Aside from this key management is a crucial issue (Behl & Behl, 2012). Often the users owning the data do not have the expertise needed to manage their encryption keys. Allowing the cloud service provider to manage the keys solves this problem but managing a large number of keys is a difficult task and the cloud service provider must have a secure way of doing this. Aside from this the entity responsible for key management must be a trusted entity. If the key management entity is not trusted by all parties the encryption might be rendered null and void seeing as there is no guarantee the keys will be kept out of reach from malicious interests (Chen & Zhao, 2012).For data used in PaaS or SaaS environments encryption is not a suitable solution. Seeing as the data has to be processed in an application it is not feasible to decrypt and encrypt the data for each computing task (Chen & Zhao, 2012). This means that data is left vulnerable to snooping co-tenants as discussed in section 4.1.1. While it has been shown that it is possible to perform some computing tasks on encrypted data it is not suitable for all types of computing (Tari, 2014).
Data integrity is a core part of managing data. Doing this in the cloud introduces new major challenges that must be solved if CC is to be considered secure. This is due to the fact that cloud servers are distrusted in terms of both security and reliability. The data stored in the cloud may be corrupted by both administrative errors as well as malicious attacks (Xiao & Xiao, 2014). Many cloud providers charge a fee for the uploading and downloading of data. This means that downloading large sections of data to verify the integrity of the data is not a viable solution. Some solutions have been proposed, including letting a trusted third party appointed by the cloud provider periodically check for data integrity. Despite this more research is needed to fully solve the data integrity issue (Chen & Zhao, 2012).
Integrity is not only concerned with data. Software integrity also needs to be taken into account. Software integrity becomes a problem since the CSP provides the applications the user utilizes. Thus it is important that the software providers have a clear security policy on how to ensure that any software used will not do unexpected things to the users’ data ( Zissis & Lekkas, 2012).
2.4.2 Deduplication
Deduplication is a technique where the server stores only a single copy of each file, regardless of how many clients requested the storage of the same file. By doing this the cloud servers as well as the network bandwidth are saved. However, deduplication may lead to leakage of sensitive side channel information. For instance a server utilising this technology might get a request to store a file, however this file is already stored on the server. The server then tells the client making the request that the file already exists in the storage, and as such need not be transferred again. This would reveal to the client that another cloud user has the exact same file, which could be sensitive information in some cases (Li, Li, Xie & Cai, 2015).
2.4.3 Loss of Control, Backup Issues and Availability
Loss of control risks are all associated with the fact that a user of cloud computing generally does not have access to the physical hardware being used. This has several implications forth users. One of the first and most important steps is evaluating if storing sensitive data in the cloud violates previous agreements with data owners (Zissis & Lekkas, 2012) (Al-Anzi, Salman, Jacob & Soni, 2014). If storing sensitive data in the cloud can be seen as a violation of the data privacy due to loss of control an organisation should not progress with their plans to move data storage and processing to the cloud. Aside from this choosing a trustworthy cloud service provider is equally important. The organisation looking to migrate to the cloud must make a careful and thorough evaluation of the cloud service providers’ security measures (Xiao & Xiao, 2013).
When an organisation stores information in the cloud the service provider could gain access to this information. This is a major threat to the organisation using the cloud. Seeing as the administrators of a cloud already have inside access preventing a malicious administrator from reading and manipulating data is no easy task. There are many solutions to this problem but no single solution can fully protect against this possibility. One solution is to never give the cloud service administrators more privilege than they absolutely need (Varadharajan & Tupakula, 2014). This would prevent them from accessing all data and functions of a cloud. Another solution is to encrypt all the data stored in the cloud. However encrypting large quantities of data might not be feasible from a performance standpoint. Therefore research has been done that suggest it might be possible to perform some computing tasks without decrypting the data. This would mitigate the performance issues as well as giving the data owner increased control of their data (Tari, 2014).
Availability is another large part of loss of control. Availability refers to the property of a system being accessible and usable upon demand by an authorised entity. The user of a cloud cannot guarantee the availability of the servers hosting the cloud. This must be done by the cloud service provider. In order to ensure data is always available the service provider and user must agree to specific specification regarding system availability (Zissis & Lekkas,2012). such an agreement should also detail who is responsible in the event of down time. This agreement should also specify any monetary compensation or similar if the target availability is not met.
Lastly ensuring data is properly secured against data loss through the use of backups also need to be specified. Keeping a local backup of everything a user stores in the cloud would be the most secure option. However this is not very economical and defeats part of the purpose of cloud computing. Just as with availability it is important to specify what is backed up, how this is done and who is the responsible party if a backup fails. It has been noted that there is a risk that the user and data owner will suffer the full responsibility if data loss occurs, with no liability for the cloud service provider (Khalil, Khreishah, Bouktif, & Ahmad, 2013).
While technology can make backups more secure the best way to establish reliable backups is to ensure that there is a clear agreement between the user and the service provider. The agreement should specify how the service provider will ensure that backups are being created and stored in a secure manner, as well liability in case of faulty backups.
2.5 Cloud Security solutions
2.5.1 Various Path of Solutions in Cloud Security
Al-Anzi, Yadav & Soni (2014) suggest a security model for CC comprising governance, risk management and compliance. CC security requirements vary quite significantly from traditional environments because of its dynamic nature and customer ownership. It is pertinent to mention that this model can be applied to each type of cloud, e.g. private, public, hybrid and community as well as the different type of services; IaaS, PaaS and SaaS. Fig. 2 presents an overview of the security model and below it follows an elucidation.
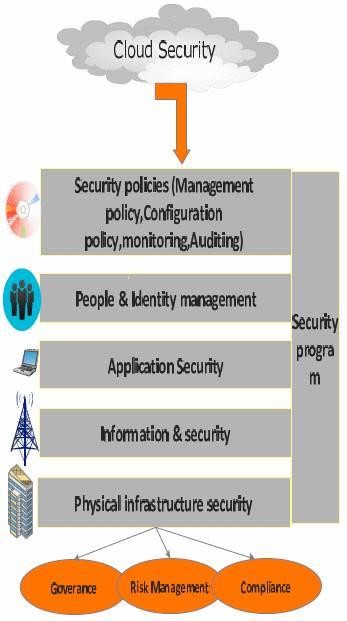
Figure3: Thesuggestedsecuritymodel (Source:Al–Anzi,Yadav&Soni,2014)
2.5.1.1 Security Governance, Risk Management and Compliance
The fundamental responsibility of the organisation is to identify and implement process, control and organisational structure so that effective security could be achieved. Governance is any set of policies, laws and technologies that work within an organisation and provide direction in order to achieve security objectives. Al-Anzi, Yadav & Soni (2014) suggest that an organisation should implement a framework for effective risk management and measure the performance of the risk management by metrics.
2.5.1.2 People and Identity Management
Only authorised users should be able to access assets, an identity federation approach is applied in order to achieve secure authentication and authorisations.
2.5.1.3 Application Security
An XML signature as well as an XML encryption is implemented in order to protect applications from XML attacks and other web service attacks.
2.5.1.4 Information Security
Data and information security is a top concern for any CSP as well as the customers using the service. As such, Al-Anzi, Yadav & Soni (2014) suggest that CSPs need to focus on how data is stored, processed and audited. In addition, they recommend an implemented intrusion detection and prevention system.
2.5.1.5 Physical Infrastructure
For physical measures they suggest the implementation of biometric access controls and a computer based access control system (CAS) which in short, restricts access to users who can provide authorisation.
2.5.2 Auditing in Cloud Security
Auditing within a CC environment basically refers to the process of ensuring data integrity of outsourced data and save the user’s computation time and online burden of additional processing. Rewadkar & Ghatage (2014) propose a privacy-preserving third party auditing (TPA). TPA will verify the storage correctness of the outsourced data periodically when the users initiate a request for verification. The goal of the TPA is to reduce the burden of users by saving their computation resources while ensuring the correctness of their data stored in the cloud.
The problem that could arise by choosing not to use TPA is that CSP’s, for monetary reasons, may delete data that is not being used or they may hide the data loss incidents to maintain reputation. Of course the user has the option of verifying this data themselves, albeit these options are impractical or risks the confidentiality of the data (Rewadkar & Ghatage, 2014).
The proposed solution will perform the auditing on the user’s request. This will be done by sending the verification metadata from the user to the server and the response will then be verified by the TPA. It also includes a so called ‘batch auditing’ which will decrease the response time for audit requests when sent by multiple users (Rewadkar & Ghatage (2014). Own test-environment showed that this batch auditing decreased the request time from 1210 ms to 80 ms another form of auditing is achieved by implementing a so called Trusted Third Party. (TTP) which, in cryptography is an entity which facilitates secure interactions between two parties, e.g. a user and a CSP (Zissis & Lekkas, 2012).The TTP reviews all critical transactional communications between the parties. Implementing a TTP in a cloud solution can address the loss of the traditional security boundary by producing trusted security domains. In short, a TTP will take advantage of Public Key Infrastructure (PKI) to ensure strong authentication, authorisation, data confidentiality, data integrity and non-repudiation (ensuring that no entity in an electronic transaction can deny its participation) (Zissis & Lekkas, 2012).
2.5.3 Policies in Cloud Security
Policies are often used as a way to ensure that organisation wide security targets are being handled the same way across the organisation. While policies on their own cannot solve security issues they are an important management tool. Cloud computing is no exception to this. When creating a policy regarding cloud computing it is important to remember that the cloud service provider must be aware of the policy. Indeed it might be wiser to develop a mutual understanding of the policy together with the service provider (Behl & Behl, 2012). This is also important due to the fact that the CSP might have several customers with different security needs and therefore it might be impossible for the CSP to create a policy that covers all the security needs of all the customers. Instead it is wiser to create policies that deal with individual customers and their specific needs (Sabahi, 2011). Ultimately a policy is only effective if the organisation owning it continuously develops secure practices using the policy as a base. Whether it is porting an existing policy or creating a new one policy alone cannot not solve the security issues all cloud users face.
2.5.4 Biometrics in Cloud Security
In many cryptographic systems the key to success lies on the client side, where cryptography and decrypting is stored. If this client in turn is attacked and hijacked by an aggressor, the whole cryptographic system is in critical condition have described ICMetrics technology as the possibility to produce unique identifiers based on the electric system’s behaviour which can then be used as a key. However, Tahir et al. (2013) argue that low entropy and a short key length for the ICMetrics key might make it sensitive to attacks. Thus, the authors suggest that this key has to be reinforced before it can be implemented as a security solution. This would be done using the cryptographic algorithm SHA-2. If SHA-2 is applied to the ICMetrics key it would provide the key with sufficient length and high entropy. Biometrics can also be used in order to create and store various cryptographic keys. By implementing ICMetrics/Biometrics as a security solution, each individual VM running on a host computer can be encrypted in a unique manner which in turn would solve the virtualization risks VM-hoping and VM-escape. VM hoping and VM-Escape are two newly derived virtualization threats. VM-hoping basically means that an attacker may use one VM to spy on another VM within the same physical host whereas VM-escape is the process in which the attacker takes control of one VM and in turn also takes control of the host-computer as well as every other VM stored on the host-computer (Rahman & Cheung, 2014 b).
2.5.5 Hardware as a Service in Cloud Security: Physical and Virtual Hardware on Demand
Cloud computing has already been adopted in a broad range of application domains. At the same time, domains such as the distributed development of embedded systems are still unable to benefit from the advancements of CC. A common obstacle is often the incompatibility between such applications and the cloud (Stanik, Hovestadt & Kao, 2012). A solution to this problem is in the form of a novel cloud layer, HAAS. This additional layer allows for usage of distinct hardware components through the Internet analogously to the cloud services. This way, HAAS will not only enable interconnection of physical systems but also virtual hardware emulation. By making emulators accessible as HAAS services, the emulated hardware components will appear to be connected to the local computer just like physical hardware normally would. For software developers this means that developed software can be tested against hardware long before the first hardware prototype has been developed, resulting in saving both time and money. As such, it would benefit the cloud service, PaaS, enormously. Since these devices will appear to be attached to a local system, arbitrary hardware devices can be virtualized using HAAS as well as specific software can access such virtualized hardware devices even though they have not been designed for being used in a cloud specific context. By using a virtual bus, multiple hardware devices can be connected even if these devices are distributed over multiple geographical locations or multiple organisations (Stanik, Hovestadt & Kao (2012). It is therefore also a viable option to implement in a community based cloud environment as well as the other type of environments, i.e. public, private and hybrid.
3.0 Practical Contribution of cloud Computing and Cloud Security
3.1 Contribution in Business Environment
What is the reason of moving many businesses into the cloud? The key reason of their moving to cloud computing is that it can enhance the efficiency and improve the cash flow along with offering several other benefits. Providers of cloud computing can deliver various applications for online business which can be accessed from servers with the help of Hybrid cloud web browser. Combination of private and public cloud is known as hybrid cloud. With the help of hybrid clouds infrastructure, private cloud security can be combined with the cost-efficient, scalable and powerful public cloud attributes. Many companies are likely to adopt the hybrid cloud deployment model as it has become main stream these days. There are a range of benefits offered by cloud computing that includes a reduced complexity, wiser shift from capital-intensive to operational cost models, greater agility and overall less cost. This can give an addition of high value to businesses and several activities that support innovation in business with low potential risks. PaaS solutions help to increase deployment of application through the effective testing and development methods. At the same time, it also enables the businesses to minimize the IT costs (Dinh, 2011).
3.2 Application
In today’s world of business the security means a lot as we see growing companies spend most of their capital in cloud security or security measures as in this report the literature review of cloud security gives us the brief information of security issues the business face it can be a small scale or big companies.
Thus the below graph show us the aspects which is mainly covered by cloud security to give the entrepreneur a big revenue growth in their business.
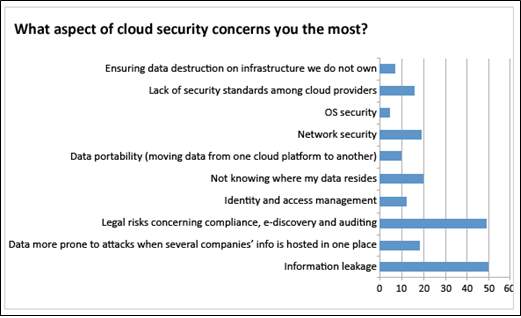
Figure 4: Graph of Services Cover by Cloud Security(LifeiWei, 2014)
3.3 The List of Companies Uses and Provides Cloud Security
- Microsoft
- IBM
- Amazon
The companies listed above uses cloud security as major aspect of their business as they provide us the applications and protects the data thus the working and the infrastructure of one of these companies is explained further.
The figure below shows us the providers of the cloud security which is widely used by many of the business.
Figure 5: Various Applications for Cloud Security(Almorsy, 2016)
3.4 Google Security Layers for Users
Google cloud platforms provide various cloud services and help the user to keep save their data from an individual point and from a business perspective thus the below diagram show us the infrastructure of google security platform
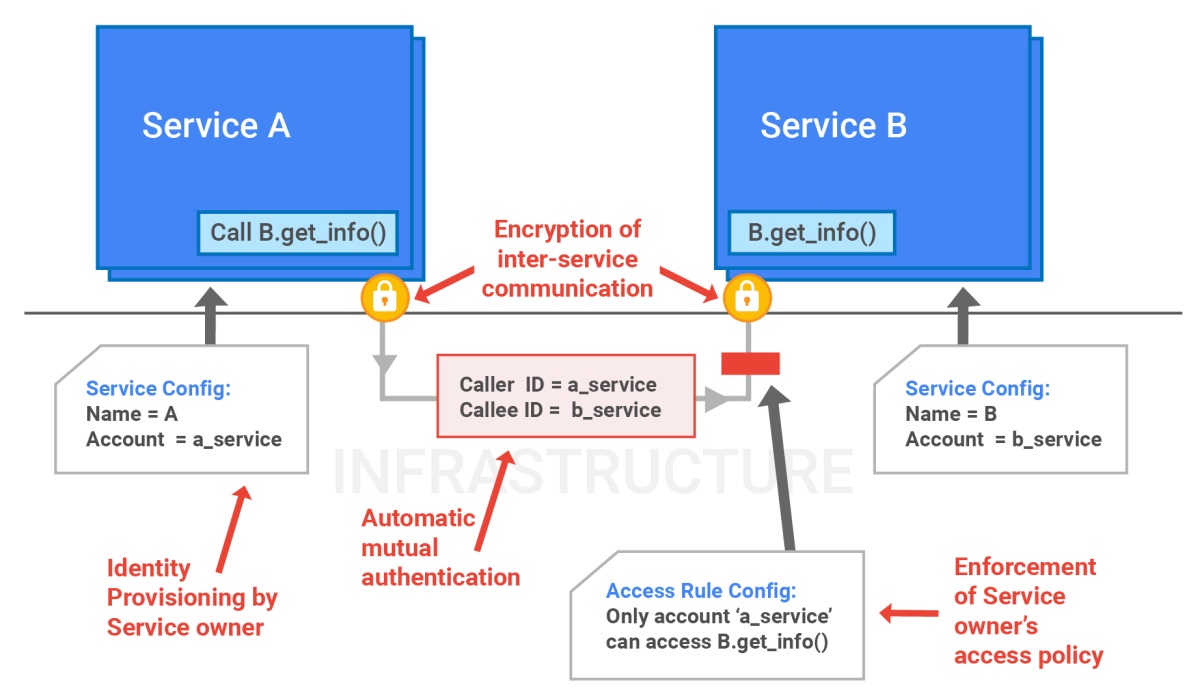
Figure 6: Google Cloud Platform Architecture(Sanaei, 2013)
The figure above show us the working of google platform how the services work thus the encryption of the data to communicate and provides a secure browsing thus this cloud platform provided by google is widely used by many companies and government authorized organizations as well thus the use of the service includes the DOS protection of file the service is use by public organizations like Colleges, Government firms, Small scale business and many more.
3.4.1 Continuous Delivery of Google Cloud Security
Applications can be updated with the help of continuous delivery from the backend and thus delivered continuously to the end users even if the users are in the mid of using the applications. Continuous delivery is very demanding as there is an increase in the complexity of online applications which require new updates on daily basis. The advantages of continuous delivery are more engaged users and the entire application performance. It also helps in reducing the time required to resolve the bugs and also minimize the repetitive tasks.
4.0 Analysis and Discussion
During the process of analysing the literature, the authors’ of this review made a discovery. It appears as if literature that discussed a certain security topic often chose to focus on only one of the affected security areas. In the area of integrity the majority of the literature focused on data integrity whereas sub-areas such as software integrity and hardware integrity were basically non-existent.
This observation that the majority of the literature neglected sub-areas of their respective research could be considered a serious threat to the future of cloud computing. Another example is physical security. Physical is often mentioned in the literature; however it is seldom seen as a major security risk. Malicious or ignorant users are also often overlooked. While it is mentioned in a small part of the literature it is possible this particular risk is often overlooked due to how broad it is. Seeing as a malicious or ignorant user can be considered a threat in all areas of an organization it makes sense that it is not seen as a key threat in literature focused on a specific risk. The final example of this is the different service models and deployment models. Almost all of the literature included a definition for the different service models. Despite this only a small part of the analysed literature attempted to distinguish unique security issues and solutions for each of the different service models. As the service models are a core part of cloud computing the authors’ of this review consider this a major weakness in the available literature. The same can be said for the different deployment types; however the lack of discussion surrounding the different deployment types is not as severe of a flaw as it is in regards to the service models. This is due to the differences between the types of deployment being more obvious. For instance a public cloud is obviously more vulnerable to malicious users since the organization providing the cloud cannot maintain control over who use the cloud. Compare this to a private cloud where the cloud provider has a greater control over who gets access rights.
The lack of literature on these sub-areas can be explained in a few different ways.
First, there is research conducted in these areas but it might not be published as a topic related to cloud computing security. For example the article related to HAAS written by (Stanik, Hovestadt & Kao 2012) is published under cloud computing but not security or cloud computing security. Second it might be possible that the sub-areas omitted from the majority of the research are not deemed important enough to warrant an entire paper. However it is most likely a combination of these reasons.
5.0 Findings
What security risks and solutions arepresented in the literatureregarding cloudcomputing security?
It is clear that there is plenty of available research regarding cloud computing security. Even so, this review proves that it is still one of the predominant issues with the technology in its entirety. This review has managed to identified several significant security threats related to virtualization and multi tenancy, data privacy and integrity, denial of service, deduplication, user access control, loss of control, backup issues, availability, trust management and security in the different service models. The review also identified several different solutions to some security risks in the reviewed literature. The identified solutions were security models, auditing, policies, SecCloud, RAID, biometrics, self-destructing data and hardware as a service.
What are thedifferencesin securitybetween public, hybrid, communityandprivate clouds as wellas theservicemodels; IaaS, PaaS, SaaS andHaaS?
One important trend in the reviewed literature is the absence of research related to the differences in security between public, private, hybrid and community cloud deployment models. This is partially due to the fact that it seems many issues and solutions affect all four types. It is pertinent to mention that what was mentioned in this literature regarding security differences was miniscule at best. Thus, the conclusion was drawn to not present these differences in their own respective sections.
In addition, the different service models associated with the various deployment models proved to be more common in the literature. IaaS, PaaS and SaaS all have their unique challenges when it comes to security, and it is clear that some research has been done in order to identify the unique threats and solutions applicable to the different service model. Alas, there was not enough information to draw factual conclusions. However, it would appear as if the IaaS layer greatly affects the security of the built upon layers, e.g. PaaS and SaaS.
6.0 Outcome
This review could serve as a theoretical basis for future research, showcasing the current major security issues as well as theoretical solutions. Future research should focus on practical case studies in order to validate the theoretical solutions discussed and presented in this review. Aside from this more research should be done in order to better understand the attitudes of cloud computing consumers as well as cloud service providers when it comes to security. Finally future research should strive to better understand the way the different deployment methods and service models affect the overall security of a system.
7.0 Conclusion
It is clear that although the use cloud computing has rapidly increased, cloud security is still considered as the major issue in the cloud computing environment as customers do not want to lose their data or private information as with the help of this report various issues and solution related cloud security is given in the paper and thus tis paper attempts to give a proposed solution to number of challenges in cloud security environment and thus the future cloud industry improvement are required to embrace and support holistic business risk.
References
Al-Anzi, F. S., Salman, A. A., Jacob, N. K., & Soni, J. (2014). Towards robust,scalableand securenetworkstoragein Cloud Computing.In 2014 Fourth International Conference on Digital Information and Communication Technology and it’s Applications (DICTAP) (pp.51–55).
Al-Anzi, F. S., Yadav, S. K., & Soni, J. (2014). Cloud computing: Securitymodel comprising governance, riskmanagement and compliance.In 2014 International Conference on Data Mining and Intelligent Computing (ICDMIC) (pp. 1–6).
Behl, A., & Behl, K. (2012). An analysis of cloud computing securityissues.In 2012 World Congress on Information and Communication Technologies (WICT) (pp. 109–114).
Boampong, P. A., & Wahsheh, L. A. (2012). Different Facets ofSecurityin theCloud. In Proceedings of the 15th Communications and Networking Simulation Symposium (pp. 5:1–5:7).
Bouayad, A., Blilat, A., El Houda Mejhed, N., & El Ghazi, M. (2012). Cloud computing: Security challenges.In Information Science and Technology (CIST), 2012 Colloquium in (pp.26–31).
Chavan, P., Patil, P., Kulkarni, G., Sutar, R., & Belsare, S. (2013). IaaSCloud Security. In2013 International Conference on Machine Intelligence and Research Advancement (ICMIRA) (pp. 549–553).
Chen, D., & Zhao, H. (2012). Data Securityand PrivacyProtection Issues in Cloud Computing. In 2012 International Conference on Computer Science and Electronics
A., Bouktif, S., & Ahmad, A. (2013). SecurityConcerns in CloudComputing. In 2013 Tenth International Conference on Information Technology: NewGenerations (ITNG) (pp. 411–416).
Li, J., Li, J., Xie, D., & Cai, Z. (2015). SecureAuditingand Deduplicating Data in Cloud IEEE Transactions on Computers, PP(99), 1–1.
Liu, M., Dou, W., Yu, S., & Zhang, Z. (2015). A Decentralized Cloud Firewall Framework with Resources Provisioning Cost Optimization. IEEE Transactions on Parallel and Distributed Systems, 26(3), 621–631.
Mell, P., Grance, T. (2011). TheNISTdefinition of Cloud Computing. (Artikelnr 800-145). National Institute of Standards and Technology.
Mishra, A., Mathur, R., Jain, S. & Singh Rathore, J. (2013). Cloud Computing Security. In International Journal on Recent and Innovation Trends in Computing and Communication (IJRITCC) (pp. 36-39).
Noor, T. H., Sheng, Q. Z., Zeadally, S., & Yu, J. (2013). TrustManagement ofServices inCloud Environments: Obstacles and Solutions. ACM Comput. Surv.
Okoli, C., & Schabram, K. (2010). A Guide to Conducting a SystematicLiteratureReview of Information Systems Research(SSRN Scholarly Paper No. ID 1954824). Rochester, NY: Social Science Research Network.
Rahman, M., & Cheung, W. M. (2014) a. Analysisof Cloud Computing Vulnerabilities. International Journal of Innovation and Scientific Research, 2(2), 308–312.
Rahman, M., & Cheung, W. M. (2014) b. Cloud Computing, SecurityIssues and Potential Solution by Using ICMetrics or Biometrics BasedEncryption. Intertional Journal of Advances in Computer Science and its Applications (IJCSIA) (Vol. 4: Issue 1. pp. 36-4
Cite This Work
To export a reference to this article please select a referencing stye below:
Related Services
View allRelated Content
All TagsContent relating to: "Cyber Security"
Cyber security refers to technologies and practices undertaken to protect electronics systems and devices including computers, networks, smartphones, and the data they hold, from malicious damage, theft or exploitation.
Related Articles
DMCA / Removal Request
If you are the original writer of this dissertation and no longer wish to have your work published on the UKDiss.com website then please:




